How people got used to Moqtada al-Sadr

[Published in The Boston Globe Ideas section.]
MOQTADA AL-SADR HAS been Iraq’s most recognizable villain since 2003, when he burst onto the scene as the most potent challenger to the US military occupation of Iraq. His rivals painted Sadr as a thug and an amateur, a wannabe who was lucky enough to be a member of a vaunted clerical dynasty yet nevertheless struggled to hold onto its followers.
A surprising thing has happened in the years since. After a series of violent clashes and reversals, Sadr has refashioned himself as Iraq’s premier nationalist statesman. Despite a very recent historical reputation as a corrupt sectarian warlord, Sadr today has emerged as Iraq’s standard bearer for secularism and reform. Running on an anti-corruption platform, he edged out all others to finish first in Iraq’s national elections earlier this month.
The United States, who had such trouble with Sadr from 2003 to 2008, might be expected to flinch at his embrace of the Iraqi Communist Party, and his growing political influence. Remarkably, though, US officials have stayed quiet about pivotal role Sadr now plays.
His steady expansion of power over 15 years is a sign of the importance of charisma, staying power and, most importantly, improvisation in a volatile and sharply divided region. Sadr’s case illustrates how a leader benefits from being a known quantity personally, while at the same time bending and shifting his ideology and political to accommodate the political winds.
A decade ago, the young Shiite cleric was fulminating against the Americans and the Iraqi “puppets” they had installed in Baghdad. He often wore a white shroud symbolizing martyrdom as he delivered thunderous Friday sermons. His Shiite militant followers were known for nighttime murders of Sunnis. He set out purist dictates against Western-style hedonism, prompting attacks against gays and liquor stores.
Today, he welcomes not just the communists but also the same secular Iraqis his organization used to target. Sadr’s communications team tweets out his latest edicts, which are more likely to contain anodyne pronouncements about political coalition building rather than fire-and-brimstone warnings against American meddling.
He solidified his power in the years after the US invasion through his fearsome Mahdi Army militia, and through jobs and spoils he acquired through the control of key government positions, including the lucrative health ministry. Yet during the recent election campaign, he vowed to overturn Iraq’s spoils system, which allows sectarian movements to carve out fiefdoms and pillage the state’s coffers.
When seeking to predict events in a country such as Iraq, policy experts in the United States and elsewhere routinely focus on deep-seated rifts around ethnicity, ideology, and religious doctrine. What’s easy to underestimate is the role of a troubled nation’s day-to-day domestic political environment — and the skill with which some key leaders navigate it.
Iraq’s domestic politics remain deadlier than those of most other countries, but the system there, as in so many places, rewards politicians who can read the crowd, who channel its frustration with self-dealing elites, and who avoid getting boxed in by their own past.
Sadr is now the single most powerful leader in Iraq, and he brings a more clear platform and set of ambitious national goals to the table than any other political leader. As kingmaker in the complex negotiations to form the next government, he is now in a position to set the government’s agenda with his unlikely — but politically savvy — platform of reform and secular nationalism.
* * *
Sadr’s father and uncle were revered grand ayatollahs whose teachings guided the behavior of millions of followers and inspired a generation of Shiite Islamist activists. His father was murdered by Saddam Hussein in 1999, and his fourth son, Moqtada, was considered too young and inexperienced to pose a threat. His Iraqi critics dismissed him as “Ayatollah Atari” — a reference to his love of video games and supposed lack of intellect.
He turned 30 the same year that the United States toppled Saddam and occupied Iraq. Within days of the invasion, Sadr had mobilized legions of followers. The one rival who could have challenged Sadr for leadership of Iraq’s Shiite poor and dispossessed was Abdel Majid al Khoei, an older and far more senior cleric who had fled into exile in London after helping lead an uprising against Saddam Hussein in 1991.
Al Khoei returned to Iraq in April 2003, with the blessing of Western troops, and set up operations in Najaf. Within weeks, he was murdered by a frenzied mob. His family, along with US officials, say that the killing was not spontaneous, but was carefully orchestrated by Sadr. Sadr denied the accusation and no one has ever been charged for Al Khoei’s killing.
Sadr quickly established himself as an uncontainable force in Iraq. Almost the entire Shiite establishment cooperated with the US occupation, viewing it as the quickest route to an electoral democracy that would bring power to the Shiite majority. The leading clerics in Najaf endorsed elections under America’s auspices. Opposition militias opened political offices and worked with the occupation authority.
Only Moqtada al-Sadr confronted the Americans from the beginning. He led demonstrations and recruited a militia. The Americans considered him dangerous and mercurial. Some Iraqis considered him a spoiler, creating unnecessary risks and detours along a sure path to electoral democracy.
Within a year of Saddam’s ouster, Sadr’s Mahdi Army was fighting an armed rebellion against the American military in central Iraq and the British in the south. Tellingly, Sadr already then couched his rebellion in nationalist terms. He sent reinforcements to the Sunni insurgency in Fallujah, in an effort to craft a trans-sectarian front.
In the seven years that followed, Sadr’s militia starred in some of the worst episodes of violence. They led the charge in the sectarian bloodletting that climaxed in 2006. They declared war against the central government in Baghdad, and were crushed. His political wing won a sizeable bloc in parliament and ran the health sector, winning a reputation for graft, corruption, and poor service.
Sadr retreated into exile in Iran from 2008 to 2011, where he studied with a senior cleric to try to raise his status. He shuttered his militia, and kept a low profile.
By the time he returned, the United States was pulling out its last combat troops from Iraq, and Sadr began his turn toward nationalism and reform.
Unlike other Iraqi leaders, his core following remained devoted to him personally, so he could count on consistent populist support, and votes. And Sadr displayed a willingness to adapt and change. He disavowed the extremist sectarians from his movement, many of whom left to form other militias and parties. He also heaped criticism on Iran for its meddling and mismanagement of Iraq’s interests. He fired and publicly lambasted some of the politicians in his movement who had been found guilty of corruption. And when the Islamic State surged through Iraq, he reestablished his militia (now called the Saraya Salam, or “Peace Brigades”), and joined the ultimately successful struggle to reimpose Baghdad’s authority across the country.
* * *
BY 2015, A GRAY-HAIRED and more muted Sadr had carved out a niche for himself as an anti-sectarian Shiite committed to a functional Iraqi state. That summer, protests broke out across Iraq against the government’s epic failures to provide security, jobs and even basic services like electricity. Sadr shrewdly reached out to the communists and secular reform activists leading the protests. He sent emissaries to Sunnis who felt disenfranchised from the state.
Out of those early meetings an enduring alliance took shape. He took aboard the suggestions of the seasoned reform activists, and decided that what Iraq needed most of all was fresh faces: qualified, independent professionals who could run its eroding government. The housecleaning began inside his own movement. Sadr stunned his parliamentary delegation, telling them he wouldn’t allow any of them to stand for reelection. His successful slate of candidates this year consisted entirely of “technocrats,” people with managerial experience but not any disqualifying political history. Some of Sadr’s own lieutenants questioned the move, arguing that political connections and party backing are crucial for getting things done in Iraq’s fractious and corrupt government, but Sadr was adamant.
He visited Saudi Arabia and endorsed warmer relations between Baghdad and Riyadh, vowing to balance Iraq’s position among the foreign powers with a hand in its politics and security.
There’s a certain Nixon-goes-to-China element to Sadr’s turn to secularism. Only a seasoned militant with impeccable sectarian credentials can make a turn toward pluralistic nationalism. His positions today are all the more plausible because nationalism has been a consistent thread in all his ventures since 2003 — and because he remains a secretive, illiberal leader with untrammeled authority within his own movement. His millions of followers bring him almost exactly the same number of votes during every election. His consistent promise is to seek more jobs and a bigger share of Iraq’s economic pie.
Naturally, there’s plenty of reason not to trust the cleric’s transformation. Sadr is a savvy operator, a seasoned opportunist who has shifted position over and over. He might do so again. And his alliance with the secular reformers and the Iraqi Communist Party could collapse if the next Iraqi government is formed with Sadr’s reformist blessing but still is unable to deliver better results than its predecessors.
In his new incarnation as an aging statesman, Sadr hasn’t shifted all that much. His followers have stopped the vigilante attacks against gays and liquor stores, but they haven’t endorsed social freedoms and rights, either.
In private, diplomats say they don’t expect Sadr to act as a provocateur. His rhetoric can be heated, but he’s a pragmatic politician who regularly meets with Western ambassadors.
Despite his clerical background, Sadr’s goals line up with a strange array of otherwise unlikely allies: secular Iraqi reformists, liberals, Sunnis, militants who want to integrate into the Iraqi state, even some Western governments. Sadr wants a strong government in Baghdad, which makes room for Iraqis of every sectarian, ethnic and political stripe. He also argues that Iraq’s top political jobs cannot be distributed on a sectarian basis, as in Lebanon.
Since 2003, there hasn’t been any parliamentary opposition in any of Iraq’s governments — every single party that has won votes has preferred a position in government so it can extract its share of corruption.
The test for every reformist movement is what happens when it gains significant control over the state. Fulminating against the corruption of past leaders is easy; it’s far harder to resist the temptation to take advantage when your side is in power.
Iraq’s system is so deeply distorted that only a strong jolt can change it. Sadr benefits from longevity, low expectations, and the lack of any more attractive alternative. But sometimes that’s enough.
Can a Shiite Cleric Pull Iraq Out of the Sectarian Trap?

The Shiite cleric Moktada al-Sadr at a demonstration in April against the bombings of Syria by Britain, France and the United States. CreditHaidar Hamdani/Agence France-Presse — Getty Images
[Published in The New York Times.]
May 11, 2018
BAGHDAD, Iraq — Iraq’s parliamentary elections on May 12 might seem to offer more of the same because most of the leading candidates and movements have dominated the country’s political life since the United States unseated Saddam Hussein in 2003. But the 44-year-old firebrand Shiite cleric Moktada al-Sadr is leading an encouraging transformation, which could jar Iraq’s politicians out of their sectarian rut.
Mr. Sadr inherited millions of devoted followers from his family of revered religious scholars. Both his father and father-in-law were grand ayatollahs, the highest clerical level of Shiite Islam. He cemented his status by leading a bloody resistance against the American occupation and fighting the United States-allied government in Baghdad. He stubbornly defied foreign intervention, angering both Iran and the United States. He has purged corrupt operatives from his movement.
In the summer of 2015, Mr. Sadr made a potentially historic about-face, uniting with the Iraqi Communist Party and secular civil society groups who were protesting the government’s failure to provide security against the Islamic State or even the basic necessities of life, including jobs and electricity. Together, the new alliance demanded an end to corruption.
Iraq regularly tops world rankings for corruption and suffers endemic unemployment, which is particularly high among youth. When oil prices were high, alleged corruption reached an epic scale, but the people did not receive any benefits in infrastructure, jobs or services. Even vital security services were gutted by no-show jobs, as glaringly revealed when there was no army on hand to stop the Islamic State’s sweep through Mosul and Anbar Province to the gates of Baghdad.T
Corruption has kept Iraqis poor and almost left the country at the mercy of the Islamic State. That is why Mr. Sadr’s slogan “Corruption Is Terrorism” resonates with so many Iraqis. Frustrated with a decade of failures by the rulers in Baghdad, Mr. Sadr embraced civil society groups and their agenda: civic rights, better governance, fair distribution of resources.
An important outcome of Mr. Sadr joining a nonsectarian coalition is a new strain of pluralism and tolerance. The liberating effect is visible in how Iraqis irrespective of class, sectarian and sexual identities can reclaim public spaces without fear.
One spring morning, a group of young men in bouffant hairdos and burgundy and bright green three-piece suits hung out in Qishleh Gardens near Mutanabi Street, the historic gathering place of Baghdad’s poets and intellectuals. In the local context, their attire announced them as gay men. As the men in colorful suits walked around, the clerics recruiting fighters for the Shiite Islamist militias nearby didn’t even throw them a sideways glance.
In the afternoon, some of the men in colorful suits joined an anti-corruption demonstration led by supporters of Mr. Sadr. “We all want to put an end to corruption,” said Mohamed Ismail, a 26-year-old unemployed day laborer. “We are all together.”
Three years earlier, when demagogues loyal to Mr. Sadr were exhorting vigilante attacks on men seen as gay, the pairing would have been unthinkable. Back then, Iraq was riven by difference — the sectarian-hued struggle between the Islamic State, which purported to speak for the Sunnis, and the governments led by Shiite Islamists, who claimed to represent the Shiite majority that had been oppressed under Mr. Saddam.
At the Baghdad Cultural Center, adjacent to the Qishleh Gardens, smiling volunteers from Mr. Sadr’s organization distributed fliers with his pronouncements. “Our new goal is to start an independent technocratic government,” said Majid Hamid, a 26-year-old volunteer. “We have no problem with anyone who is Iraqi.” The movement’s emphasis is now on civic questions.
After more than a decade of dominance by Islamist Shiite movements, competitors for power can no longer meaningfully distinguish themselves by their sectarian identity. Self-styled religious parties have been implicated in every major graft scandal, including the mishandling of oil revenue and defense contracts.
In early May, Grand Ayatollah Ali al-Sistani, the most revered cleric in the country, took the unprecedented step of declaring that true believers must not vote along sectarian lines and reminded voters that the clergy has not endorsed any party.
The biggest transformation of all has come during the fight against the Islamic State, which united all manner of Iraqis against nihilist fundamentalists: Shiite and Sunni, Kurd and Arab, Muslim and Christian, religious and secular. Every major electoral faction includes a mix of Iraqis, and the ideas of nationalism and secularism are slowly returning to the Iraqi political sphere.
Prime Minister Haider al-Abadi, who has roots in the secretive Shiite Islamist Dawa Party, has positioned himself as a nation-builder who thwarted challenges from Sunni supremacists and Kurdish separatists but is willing to accept any patriot as a member of his coalition. Even the most militant Shiite militias have included Sunni partners in their electoral coalitions, including the Fatah Alliance, led by Iran’s fearsome ally, Abu Mahdi al-Muhandis.
Mr. Sadr has ordered his followers to support the idea of a secular, nationalist government run by “technocrats,” experts who are not career politicians and supposedly will be able to solve Iraq’s ills. He touts the importance of the rule of law and civilian power.
In a series of interviews with politicians, analysts, fighters and citizens, I repeatedly heard that a broad range of Iraqis believe they are at the beginning of a “nationalist moment,” when the country’s political culture might be transformed for the better.
Mr. Sadr has reinvented himself countless times in an erratic political career and can be a fair-weather ally. His appreciation for new, secular allies is not an endorsement of liberalism or progressive views.
But Mr. Sadr has always been a nationalist, committed at least in rhetoric to unifying patriotic Iraqis regardless of sect or ethnicity. His current campaign for a civil, anti-sectarian, reformist government raises hopes and possibilities not experienced in recent Iraqi history. He is changing the terms of political debate.
His political lieutenants say they want to lead the Iraqi government, or else serve as a vigilant parliamentary opposition. Since 2003, every faction that won a share of votes opted to join a broad coalition government and extract its share of the spoils from the public sector trough.
Mr. Sadr shows that a political movement known for the exploits of its militia and corruption can also become a standard-bearer for root-and-branch political reform. His unlikely reformist alliance could give Iraq’s political culture the jolt it needs.
Thanassis Cambanis, a senior fellow at The Century Foundation, is the author, most recently, of “Once Upon a Revolution: An Egyptian Story.”
Can Militant Cleric Moqtada al-Sadr Reform Iraq?
[Read the full report at The Century Foundation.]
In the fifteen years since the American invasion toppled Saddam Hussein from power, Shia cleric Moqtada al-Sadr has distinguished himself from other emerging Iraqi leaders with his endurance, iconoclasm, and unpredictability. He has cut a bedeviling and at times magnetic figure in his country, and he is one of the few sectarian leaders whose popularity has crossed sectarian lines.
Through war, flips of allegiances, involvement in corruption, and military victory and defeat, Sadr has managed to preserve his maverick image as a stubbornly independent man deeply committed to his principles, even as those principles shift over time. Now, with the May 12 Iraqi elections approaching, he is trying to parlay his reputation as a nationalist free-thinker into a movement that can transform Iraq’s political system.
In fact, Sadr has fashioned himself into an unlikely tribune of reform in Iraq. A persistent thorn in the side of foreign powers and Iraqi politicians alike, the graying forty-four-year-old is now trying to radically reshape his country’s politics. He has freshly renounced religious sectarianism, building an alliancewith Communists and secular reform activists.1 He has attacked Iraq’s corrupt spoils system, with slogans such as “corruption is terrorism” that resonate with millions of disenchanted Iraqis. His unorthodox electoral campaign joins Shia partisans, Communist ideologues and some of Baghdad’s secular elite. Sadr’s popularity, hard power, and unifying message make him a direct threat to Iraq’s political class.
Even though his movement is unlikely to win a majority, Sadr’s unique campaign and nationalist-religious-secular alliance has upended nostrums about Iraqi and Middle Eastern politics. He hopes to establish new guiding principles: Sectarian movements can change their politics and become secular and nationalist. Armed militants can take part in electoral politics and government. Sectarian constituencies can embrace nonsectarian principles and support power-sharing and coexistence.
The evolution of Sadr and his movement has unfolded along pragmatic lines, with many flaws and inconsistencies. Nonetheless, Sadr’s political makeover amounts to a groundbreaking and encouraging transformation. It compels other established movements in Iraq to address the core challenges of security and governance, while building trans-sectarian or nationalist coalitions. He sets an example for other leaders and political organizations interested in exiting the confining boxes of sectarianism and patronage and mobilizing broader, more fluid and inclusive idea- or policy-based movements.
The success of Sadr’s approach and platform is more important than that of his candidates. If his coalition is repudiated by voters, or abandons its plans to challenge poor governance, then we can expect more of the dispiriting business-as-usual from Baghdad. But if Sadr follows through after the election and promotes the formation of a platform-based government with a legislative opposition, then we can expect Iraqi politics to enter a new phase, moving away from narrow sectarianism and patronage-only politics. A transition to a government with some technocrat ministers, a real opposition, and some pretense of nonsectarianism is necessary if Iraq is to begin addressing policy problems that affect the stability of the entire Middle East. The most pressing concerns include securing and developing the areas liberated from the Islamic State and reincorporating Sunni Arabs and Kurds into Baghdad’s fold.
This report traces Sadr’s evolution, and both the perils and promises of the road ahead. It is based on more than forty interviews conducted in Iraq in February and March 2018, with support from a grant from the Carnegie Corporation of New York.
Charismatic Provocateur
Iraqis have long bemoaned a lack of leadership and vision within the ruling class. The melee of corruption and militia-formation that has plagued Iraqi public life since 2003 has featured a parade of politicians and warlords, many of whom have evolved into effective operators. Yet only two indisputably strong, charismatic leaders have distinguished themselves from the fragmentary society of party bosses, warlords, tribal leaders, and the grifters and opportunists who have made deals with the wardens of cash. Those two are both Shia clerics, and no love is lost between them.
The first, and most influential, is Grand Ayatollah Ali Sistani, the single most authoritative leader in Iraq. A cleric of impressive intellect and conservative (rather than radical) nationalist views, Sistani is credited as a moderating force who at times kept Iraq from civil war and at others helped mitigate the scope and damage of sectarian conflict.
The other enduringly powerful figure is the far more junior Sadr, who in the wake of the U.S. invasion emerged as a strong counterpoint to Sistani’s style of leadership and modest ambitions. Sadr lacks the educational pedigree of the ayatollahs who are considered “marjaiya,” or sources of emulation, and whose teachings are followed by millions worldwide. Still, Sadr inherited the millions of passionate followers of his father and uncle, both revered ayatollahs; and he also continued the family feud against Sistani, whom the Sadrs regarded as too timid.
Sadr was not yet thirty years old when the United States invaded Iraq. His family organization already included a nationwide network of staff and offices, and Sadr quickly leveraged these to assemble a committed militia, the Mahdi Army. He emerged as a powerful and unpredictable force—violently opposed to the American occupation as well as to homegrown Sunni extremists.
Although he is a Shia cleric, Sadr made it clear with his rhetoric and style that he was first and foremost an Iraqi nationalist, not beholden to foreign powers, whether Iran, the United States, or another country. From 2004–08, the Mahdi Army forged a fearsome record of violence, fighting at different times against U.S. forces, Sunni sectarians, and fellow Shia movements. His fighters rallied, at least initially, under the banner of resisting the American occupation. In the first years after Saddam’s fall, the Mahdi Army and the Sadrist political organization made symbolic overtures to non-Shia resistance groups and expressed a willingness to ally with Iraqis of any sect or ethnicity (a commitment evident more in rhetoric than in practice). As a result, and especially in the early years following the invasion, Sadr was one of the few militia commanders who enjoyed at least some grudging respect across sectarian lines. The ensuing decade dulled his sheen somewhat, as his soldiers were implicated in some of the same abuses and sectarian violence as other factions, and his political partisans, the Sadr Movement, proved every bit as susceptible as other parties to the temptations of corruption. In 2008, Sadr officially disbanded his Mahdi Army militia, although much of its structure and membership survived in other guises within the Sadr organization. In 2014, in response to Sistani’s call for fighters to resist the Islamic State, Sadr launched Saraya al-Salam, (“Peace Companies” or “Peace Brigades”), a successor militia to the Mahdi Army which included most of its veteran officers who hadn’t moved on to other, more militant organizations.

Sadr’s trajectory has not been a simple one-way ascent from militia strongman to political player. His story abounds with course-changes and seeming contradictions. For example, he has witheringly attacked the Iraqi political system, even as he has deeply embedded his politicians within it. And though in 2018 he has mounted a new campaign against corruption, throughout the post-invasion years, Sadrists won a hard-earned reputation for epic corruption in their government fiefs, including the lucrative and critical health ministry which they controlled from 2006–07.
Unlikely Partners for Reform
In 2015, the rise of the Islamic State shattered the business-as-usual trajectory of Iraqi politics. Sectarianism had flourished, along with the corrupt spoils system. But foreign influence on Iraqi politics, along with security services crippled by corruption and no-show ghost soldiers, was no match for the Islamic State. Many Iraqis already had reached a breaking point because of raging unemployment and the government’s failure to provide basic services like electricity. Basic services had never been fully restored since the American invasion of 2003, despite years of banner oil profits, mostly lost to corruption. Protest camps sprung up around the country. In Baghdad’s Tahrir Square, followers of Sadr got to know followers of the secular reform parties, including the Communists. Over time, trust grew. Leaders of the secular parties were invited to meet with Sadr.

By the time the Islamic State shattered Iraq’s sense of security, Sadr was already changing course. With the protest movement, he adopted a newly moderate and inclusive rhetoric. Sadr threw his weight behind the protesters. He encouraged his political movement and followers to make common cause with secular reformers and independent technocrats. His followers ceased their very public attacks on homosexuals. “He has undergone a change, an evolution,” said Raid Jahid Fahmi, the secretary general of the Iraqi Communist Party, who has led the secular embrace of the cleric Sadr. “You will find a change in his vocabulary and thinking.”2
“Sadr is ready to cooperate with anyone with Iraqi interests,” said Fahmi. “This was a very important cultural shift.”3
After joining forces with protesters from other factions in 2015, Sadr and his top lieutenants repeatedly met with potential partners. Over time, leaders in the Iraqi Communist Party and the Iraqi Republican Party, led by a secular Sunni pro-American businessman named Saad Janabi, grew convinced they could trust Sadr—and that they would be given an equal role in designing the alliance, even though their parties were much smaller than Sadr’s following.4
“Moqtada al-Sadr is the only person who can summon one million people with a single call,” Janabi said. Secular Iraqis and even some sectarian Sunnis have come to believe Sadr’s nationalist rhetoric, he added.5
In coalition with his new partners, Sadr said he would support an entirely new group of technocratic candidates under a new name. He disbanded his existing “Ahrar” parliamentary bloc, with thirty-four members. He ordered them all not to run for reelection, clearing the way for a new slate of technocrats—the vague term of choice for Sadr and his movement to describe the putative category of professional, independent experts who they believe could improve the Iraqi government’s performance, unfettered by sectarian or political allegiances. Sadr’s new party is called “Istiqama,” which means “integrity,” and the overall coalition with the Communists and other smaller members is called “Sa’iroun,” which means “On the move,” or “Marching,” with the intention of evoking a march toward reform. The alliance’s goals are clear: a civil, secular state, run by technocratic experts who can fight corruption and improve governance.

Sadr’s New Platform in Context
Sadr’s record makes his positioning today all the more interesting. In the pivotal 2018 parliamentary elections, he has declared himself the leading opposition reform candidate. Some of his new claims strain credulity because of his checkered record, but his sheer power and loyal following mean he always has potential as a kingmaker. Electoral math makes unlikely his ambitions of winning the prime minister’s job for his political movement, but he is establishing an entirely new style of politics and rhetoric, which holds critical promise for Iraq and possibly for the entire region.6 First, he has fashioned a potentially inclusive national narrative from the grisly history of sectarian violence that has buffeted Iraq since 2003. Second, he has deftly eclipsed paralyzing political binaries, by forming an alliance with the Iraqi Communist Party and a small array of independent, secular reformists. Third, he has spurred an open discussion of the central problem of Iraqi politics: the “muhasasa” system, most accurately rendered as the “allotment” or “spoils” system.
“This alliance is something new,” said Fahmi, the Communist leader, who has led the secular embrace of Sadr.7 “The political process must shift to a citizenship state from a constituency state. The sectarian quota system is incapable of giving solutions to the problems of the country.”
Since the fall of Saddam’s dictatorships, elections have done nothing to dent the sectarian-based patronage structure in which there is no opposition to the government, but only a shifting free-for-all to feed at the public trough. Elections merely determine what share of power each party gets—the more votes a party secures, the more profitable the ministries to which it lays claim. No successful party has ever refused to take part in the government, joining in the broken-piñata frenzy of corruption that has characterized Iraqi governance at least since Saddam’s era.
The 2018 elections come at a moment when much has changed in Iraqi politics, and Sadr has carefully shaped his movement to make the most of it. The upcoming vote arrives on the heels of a successful military campaign against the Islamic State (in which Sadr’s fighters played an important role), and the coming of age of Iraq’s Shia sectarian militias and Islamist parties. The Shia Islamist militant parties have dominated Iraq since 2003. They have defeated their main external rivals and corralled Kurdish separatism. They have fought each other, sometimes in bitter political contests and at times in outright war, as in 2008 when Prime Minister Nuri al-Maliki drove Sadr’s Mahdi Army out of Basra. Today, being a Shia Islamist militia no longer serves as a politically distinguishing identity. All the major electoral coalitions are led by Shia politicians, and most include some Sunni and Kurdish partners and candidates. Fissures within the Shia political space have strengthened other layers of political identity. Politicians now distinguish themselves by their approach to securing Iraq in the future from a resurgence of the Islamic State; balancing the influence of Iran, Saudi Arabia, Turkey, and the United States; and solving the nagging problems of poverty, development and corruption. While other Shia political parties are experimenting with nationalist identity in the wake of the campaign against the Islamic State, Sadr has been identifying as a nationalist for years. He stands out further still by his vigorous support for the idea of a civil, even secular, state.
Security officials still worry about continuing threats from the Islamic State, but according to some Iraqi analysts voters have already moved on. Polling, they say, shows that Iraqis are more concerned about livelihoods than anything else. “Security is no longer a priority,” said Sajad Jiyad, head of the Bayan Center, a think tank in Baghdad.8 “They’re asking for jobs, not for security.”
Yet even as Iraqi politicians pivot to face these new voter priorities, the electorate is meeting them with increasing suspicion and cynicism. Sadr has presented himself as something of a political outsider—and certainly not one of the Baghdad elite. His reinvention as a coalition builder enhances his appeal, suggesting he means it when he says he is ready to do business in a new way.
“The state is failing,” said Dhiaa al-Asadi, leader of the current Sadrist bloc in parliament and a political operative very close to Sadr.9 “The existing political elite are part of the problem. They can’t be part of the solution.”
Sadr wants to see the militias formed to fight the Islamic State fully reintegrated into Iraqi government control. He wants sectarian quotas abolished for public sector jobs and government positions. He wants a carefully balanced foreign policy that keeps Iraq equidistant from Iran, Saudi Arabia, Turkey and the United States. He has also been one of the only important Iraqi Shia leaders to oppose the involvement of Iraqi Shia militias in the Syrian civil war.10 He wants to come to terms with separatist Kurds. Above all, he wants to jumpstart the moribund economy to provide jobs and salaries to Iraqis—the poorest of whom are disproportionately part of Sadr’s following.
In this context, Sadr’s frontal challenge to the central narratives of Iraqi governance since 2003 has the potential to force the ruling parties to shift their rhetoric and approach. Indeed, the process can already be seen in action.
Bridging Old Rifts
Take, for example, Sadr’s changing relationship with Prime Minister Haider al-Abadi, who, despite reservations about Sadr that have at times erupted into violent confrontation, has continued to court and collaborate with the cleric. Abadi has gone so far as to adopt some of Sadr’s rhetoric. One billboard at the entrance to Baghdad shows Abadi’s face and reads, “corruption and terrorism have one face,” echoing the Sadrist protest slogan, “corruption is terrorism.”
Abadi’s wary embrace of Sadr is especially significant given that the many of the latter’s supporters view Abadi as a villain. One recent demonstration, in February, marked the one-year anniversary of the death of fourteen demonstrators—killed at the hands of Abadi’s security forces while marching toward the Green Zone. Marchers carried flag-draped coffins commemorating the “martyrs for reform” in the same manner that they would honor martyrs who died fighting the Islamic State.
Abadi and his allies have opted to accept Sadr as a potential partner, although Sadr’s critical rhetoric has made them wary. “I think we should distinguish between the election campaign and the reality,” said Sadiq al-Rikabi, a member of parliament and a close ally of the prime minister.11 “It is very easy to stand against corruption,” he added, but much harder to articulate tangible policy proposals.
Perhaps even more significant than Sadr’s partial rapprochement with Abadi is that with Sistani. Despite Sadr’s persistent popularity, Sistani’s influence remains more important—but also more diffuse. Sistani’s clout with Iraqi Shia is not absolute nor instrumental; he doesn’t directly control any political parties or militias, and despite his extensive efforts, he has been unable to persuade Shia politicians to avoid corruption, violence and sectarianism. Still, his edicts hold force. It was a fatwa from Sistani in 2014 that created the popular mobilization units (“al-hashd al-sha’abi,” or PMUs). Almost all Shia in Iraq heed Sistani’s edicts, and he has been credited on multiple occasions with limiting the deleterious impact of Iraq’s worst crises. Sistani has telegraphed his disappointment with the record of the Shia Islamist parties that have dominated Iraq’s government since the 2005 elections. The Shia parties almost uniformly try to claim the approval of Sistani and the other senior Shia clerics, even when Sistani has made clear that he supports none of them. Sistani warned leaders of the Shia militias not to parlay their battlefield success into political campaigns, but most of them ignored the order, to Sistani’s chagrin.
In an interview, a representative of Sistani criticized militia leaders for seeking “political advantage” from the “blood sacrifice” that Iraqis of all sects made in the resistance against the Islamic State.12 As the parliamentary campaign has heated up, Sistani has made his displeasure even more clear. One cleric close to Sistani went on Furat Television to warn voters not to make their choice based on sect.13 “The corrupt people we have voted for have robbed the nation. We ought to not vote for them again, even if they are members of our clan or sect,” said the cleric, Rashid al-Husseini.14 “I would rather trust a faithful Christian than a corrupt Shia.”
Historically, Sadr has been at odds with Sistani and the other senior clerics in the marjaiya. In the current campaign, however, he has closely shadowed Sistani’s pronouncements about corruption and the need to elect new leaders. In recent statements, Sadr has addressed skeptical voters who have lost faith in the political process because of the corruption and failures of previous Iraqi governments, including those with the participation of Sadrists. “We will not be deceived by the lies again,” Sadr wrote in an April 14, 2018 statement.15 His own movement’s previous failures, he said, “give the motivation and determination to succeed in this election.”
On April 4, 2018, Sadr released a series of arguments against boycotting the elections. “Some ask, and say: the corrupt and the old faces will stay in power whether we vote or not,” Sadr wrote. He offered thirteen rebuttals, evoking religious loyalty, patriotism, optimism, and the responsibility of citizenship.16
In today’s Iraq, Sadr boasts a unique status.17 He can count on nearly absolute devotion from his rank-and-file followers, his organization, his political party and his militia. Even Sadr’s opponents recognize his political heft. In this, he is different from other Iraqi religious leaders only in degree: Mowaffak al-Rubaie, a former national security adviser who is close to several senior Iraqi politicians, said that millions of Iraqis venerate clerics and will do whatever those clerics instruct.18 During a visit by Sadr to the Kadhamiya shrine in Baghdad, Rubaie recalled, Sadr’s followers crowded the cleric’s jeep to touch the dirt on its wheels, which they smeared on their heads as a blessing. “If he orders these people to set themselves on fire, they will do it,” he said.
Sadr’s positions have appealed to Iraqis who are weary of conflict but seek to maintain dignity and integrity in their foreign relations. For example, Sadr has softened his rhetoric about secularists, and has been willing to mend fences with Saudi Arabia and criticize Iran. But at the same time, he has maintained a hard line against the United States, whose influence in Iraq he considers wholly malign.
The fact that those positions are accommodating while remaining tough and without being overly compromising—much like his evolving relationships with Abadi and Sistani—make his calls for unity that more meaningful.
“Healing is gradual,” he said in the April 14 statement. Iraq has never before experimented with professional technocratic politicians, “without any partisan or religious or ideological or ethnical indications, to choose the most effective and the best [leaders] for the love of Iraq, and the love of Iraq is of faith.”
Managing Expectations
If this account of Sadr’s well-timed transformation into a champion of nonsectarian political reform sounds a little too gung ho, there are plenty of structural and historical reasons to readjust expectations to a more realistic level.
The results of the May 12 election are likely to set in motion a long negotiation process; many seasoned Iraqi politicians and analysts believe the outcome will be another unity government like all those that have ruled Iraq since the U.S. occupation, with goodies and power divided among sectarian parties. Sadr has pulled many about-faces before; he may tire of the alliance with secular parties, or he might decide he can better serve his constituents by joining yet another weak coalition government. “Moqtada al-Sadr has been on television and in politics for fifteen years and he has accomplished none of his goals,” said one political insider close to the government. “He has been revealed to be someone who cannot be trusted.”19
Fighting Sectarianism
Specific aspects of Sadr’s past raise questions about his sincerity. For example, despite his maverick image, he has played his part in the problem of sectarianism. The Mahdi Army orchestrated some of the worst ethnic cleansing and sectarian killings of 2006, although Sadr subsequently pulled his loyalists back. Many of his extremist supporters defected to other organizations or founded their own, like Qais al-Khazali, who is now the leader of Asaib al-Haq, a Shia militia close to Iran.
Some secular leaders never overcame their mistrust of Sadr, with his religious background and history of secrecy and political about-faces. One of the secular reform leaders who rejected the coalition is Shirouk al-Abayachi, leader of the National Civil Movement and a member of parliament.20 Sadr’s organization is “foggy” and evasive, she said. “One year ago they would call us infidels,” she said. “We don’t know what they want from us.” If the Sadrist alliance does well in elections, she said, history suggests that Sadr and his lieutenants will make the important decisions, rather than deferring to the independent secularists from tiny parties. “We don’t just want seats in parliament,” Abayachi said. “We want to build a clean alternative.”
Despite his conciliatory reform rhetoric, Sadr has been willing to turn to outright confrontation with the state. Despite his status as a junior partner in the Iraqi government, Sadr personally broke through the security cordonsurrounding Baghdad’s Green Zone in March 2016.21 His followers set up a protest camp in the heart of the government, even briefly occupying parliament and the prime minister’s office.

Pervasive Corruption
When it comes to fighting corruption, there are similar reasons to moderate enthusiasm for Sadr.
Existing anti-corruption efforts suggest it will be difficult to make meaningful inroads against the spoils system. “The system needs to be reformed but there is no incentive to reform,” said Ali al-Mawlawi, director of research at the Baghdad think tank the Bayan Center.22 “The government has hard evidence, but the corrupt judiciary won’t prosecute.”
Even Sadr’s own politicians have struggled to have an impact, and critics of Sadr’s reform program point out that it is short on specifics. Jumaa Diwan al-Badali is a Sadrist member of parliament who represents the poor Baghdad district of Sadr City (which takes its name from Moqtada al-Sadr’s father, Mohammad al-Sadr); Badali is also the rapporteur of parliament’s integrity committee, in charge of investigating corruption. His experience shows the limits of any serious effort at reform. His committee has publicized some problematic contracts, often resorting to media leaks to force the government to pay attention. Parliamentarians have uncovered kickbacks and fishy contracts in the department of defense, including one case, Badali said, where the department attempted to buy subpar and nonexistent equipment for the fight against the Islamic State.23
The biggest contract they stopped was a $2.5 billion weapons deal with China, which was part of the 2017 budget. Badali believes the U.S. encourages corruption in Iraq as a way of keeping the country and its security forces weak. “I don’t accept the prime minister’s depiction of Iraq as a pool of corruption,” he said. “We are a country with some corruption. We are not the most corrupt country in the world.”
Aside from the general difficulty of rooting out corruption, Sadr and his allies are hardly innocent of graft themselves. Sadr’s militia, the Saraya Salam (“Peace Brigades”), a PMU created in 2014 from the remnants of the Mahdi Army, has benefited from government funding. Corruption clearly played a role in eroding the combat readiness of Iraq’s security forces prior to the rise of the Islamic State, but the rise of new security institutions, including the PMUs, has only fueled the type of corrupt militia patronage that has hobbled the central government.

Over the years since 2003, Sadrist ministers and members of parliament joined the corruption frenzy as well, taking kickbacks and doling out patronage jobs through ministries under their control. Sadr’s principal secular ally, the Iraqi Communist Party, also enjoyed influence through the spoils system, winning positions in the cabinet despite very winning very few votes. Fahmi, the current Communist leader, served as minister of science and technology from 2006 to 2010. Fahmi preserved his reputation for probity through his time in government, although—critics of the Sadrist reform project are quick to point out—he wasn’t able to roll back corruption by other parties in government.
“Who can fight corruption?” said Ahmed al-Krayem, a tribal leader and provincial politician who alleges that Sadr’s followers and fighters participate in the same kickbacks and extortion schemes as every other Iraqi political party and militia group.24 “The Sadrists won’t fight corruption.” Even the prime minister, Krayem pointed out, has been dogged by allegations of corruption from his earlier stints in government before taking over as premier.
Interestingly, Sadr doesn’t refute charges that his own movement is implicated in the failures of past attempts to root out corruption, but rather insists that change depends on continuing engagement and changing tactics. “We didn’t hope to be corrupted,” he wrote in answer to one supplicant who asked how Sadr justifies his political campaign given that his movement has participated in every single one of the corrupt governments since 2003. “We are rising up against the political process from the inside, rather than from the outside.”
Profound Political Problems
Some of the differences within the Sa’iroun coalition seem unbridgeable. Sadr’s Shia followers fought the United States and died in droves. Janabi’s secular followers include many elite Sunnis who are openly fond of the Americans. The Communists, meanwhile, have a long history of tensions with the clergy. Still, supporters of the alliance say these differences won’t lead to political fissures. “Sadr can control his people if there are problems. We will control our followers,” Janabi said. “We agree about fighting sectarianism.”
Another sticking point for Sadr’s agenda may be that the idea of apolitical “technocrats” who just get the job done may be something of a fantasy—at least for Iraq.
Even Sadr’s supporters point out that technocrats can only have impact if they are effective politicians. “I don’t believe in technocrats,” said Hakim al-Zamili, an influential Sadr lieutenant who runs the parliament’s security committee.25“Only a strong politician with a base in a political party can succeed. The country is full of militias, people with weapons in the streets. An independent technocrat without a political party can’t do anything.”

Independents have served as ministers in Iraq since 2003, and none has managed to change the system. The types of figures who can change the system, Zamili said, are tough political veterans with the backing of formidable parties. “Maybe a political technocrat like me can do something,” he said. “No one can threaten me, no militia. I can speak, I can interrupt someone, no one can stop me.”
Iraq’s system is broken; it might benefit from repairs, but Iraqi voters should not expect a wholesale revolution. “Let’s be honest—we can’t accomplish everything we are planning,” Zamili acknowledged.
Murder in Samarra
Power politics in Iraq can play out at a visceral level, and one recent incident has underlined both the frailty of Sadr’s new vision, and its promise.
Sadr has repeatedly taken the position that there should be only one central authority in Iraq—the state—and that all militias must be integrated into government control. At the same time, he commands thousands of militia fighters in the Saraya Salam, most of them stationed in the flashpoint shrine city of Samarra, north of Baghdad. Samarra is a mostly Sunni city that is home to one of the most holy spots for Shia Muslims, the site where it is believed that the twelfth imam went into occultation in the ninth century. Sunni extremists blew up the Shia shrine in Samarra in February 2006, setting off one of the deadliest periods of sectarian fighting in Iraq. Islamic State fighters held sway in Samarra until Shia militias drove them out in 2014.
Since 2015, Sadr’s militia has held sole control of the city. According to Sadrists and Saraya Salam commanders and fighters, their tenure in the city has been a model of success. They have formed partnerships with local business owners and tribal leaders, most of them Sunni, and have restored security and the business that comes with pilgrimage traffic. Critics accuse the Sadrists of ruling the city with an iron fist, detaining political critics, and extorting money from local traders and business owners. The accusations were repeated in multiple interviews with the author, and aren’t out of the ordinary in Iraq; in fact, the accusations levied against the Sadrist militia are much milder than those heard in zones ruled by other Shia militias, where displaced Sunnis live in fear of disappearance and, in some places, of summary execution.
The fact remains that the Sadrists are running a fiefdom, a state-within-a-state in Samarra; while such behavior is the norm in today’s fragmented Iraq, it contradicts the Sadrist platform of reforming the state under a unified nationalist banner. In March, the dangerous equilibrium resulting from so many overlapping security forces collapsed with a shootout between allies in Samarra. On Tuesday, March 13, the prime minister’s personal security detail was driving north in a convoy, preparing for Abadi’s planned visit later in the week to Mosul. The road took them through Samarra. At the town’s main checkpoint, according to two members of a committee that investigated the incident, the convoy refused to stop at the Saraya Salam checkpoint, as they are required to by law.26 Commandos from Battalion 57 of the Iraqi Army, the prime minister’s special unit, went so far as to confiscate weapons from some of the Saraya Salam fighters at the checkpoint. “It was humiliating,” said one of the members of the investigative committee that visited Samarra days later.27The angry fighters radioed ahead to the next checkpoint, a kilometer away, where Saraya Salam militiamen blocked the road with Humvees and confronted the convoy. Dozens of gleaming black sports utility vehicles swarmed the checkpoint. The army unit then fired toward the checkpoint. The Sadrists returned fire, killing Brigadier Sherif Ismail, the battalion commander and a trusted supporter of the prime minister.
Both Sadr and Prime Minister Abadi avoided public recriminations, and ultimately the killing was settled through a tribal agreement. The military unit, according to the investigative committee, was at fault for ignoring proper checkpoint procedures. “We need to develop a culture of respect,” said Zamili, the Sadr lieutenant, who was one of four members of the investigative committee. Another member of the investigative committee, who is not from either the prime minister’s or from Sadr’s bloc, blamed a lack of professionalism. “They were arrogant. They wanted to show off, they didn’t want to follow the rules,” the member said. “It was 100 percent an accident.” Political, military and economic power are inextricably intertwined, and state authority is severely compromised. This particular killing strained but did not break the alliance between Abadi and Sadr, but it revealed yet another potential point of rupture. Tellingly, it was resolved not by the judicial system or by a formal political process, but by a combination of ad hoc investigation and informal tribal justice.
Turning Point Election
The 2018 elections will set the course for Iraq’s government for at least another four years. If the current spoils system continues, with every major party joining into yet another ineffective unity government, Iraq can expect to repeat similar crises. It will be nearly impossible to maintain the effective national security approach that defeated the Islamic State—an approach that required unified command, mass mobilization, and help from all of Iraq’s competing allies, including Iran and the United States. Economic development will require warm relations with Iran, the United States and Saudi Arabia, and, at the very least, a curtailing of rampant corruption. None of these improvements will come to pass without a powerful prime minister, a meaningful opposition, and competent ministers. Sadr’s trailblazing coalition marks a crucial possibility for Iraq: the mainstreaming of civic-secular nationalism, and the passing of national politics from sectarianism into a new phase. More emphatically than any other leader, Sadr has abandoned religious and sectarian discourse, showing that a Shia cleric with a sectarian base can embrace civic, secular politics. There is, of course, ample precedent for such politics in the last century of Arab political history, but sadly, very little among contemporary Iraqi political leaders.
An informal quota system reserves the most important job, prime minister, for a Shia, and the presidency and speaker of parliament for a Kurd and Sunni Arab respectively. If this new tradition survives another electoral cycle, it will fast become the kind of pernicious unwritten tradition that cannot be changed—like Lebanon’s sectarian quotas, which have become unassailable even though they are not in the constitution.
In his alliance with Communists and secularists, Sadr has mainstreamed civic politics. If he sticks with his current course, he can also set an example for other leaders who are willing to move past their origins as sectarians, clerics, or militia leaders. Despite his pointed anti-Americanism and history of armed resistance, the United States should welcome Sadr’s new role. So should Iran, which hoped to make Sadr into one of its proteges before the cleric broke with Tehran as well. Sadr’s broadsides against the United States (his lieutenants regularly brand the Baghdad embassy as a “devil” spreading sedition and strife in Iraq) shouldn’t obscure the common interests he shares with the United States and its Iraqi partners: building a strong, effective government and encouraging a nonsectarian, inclusive national identity that can help end the cycle of sectarian violence.
Sadr’s new rhetoric, and his secular political alliance, mark one of the most promising developments in contemporary Iraqi politics. There are plenty of reasons to question his sincerity, or the durability of the partnerships he has forged since 2015, but those partnerships hold the potential to change the tenor of the entire political playing field. Sadr’s reinvention of himself from militant cleric to nationalist anti-sectarian statesman comes at a time when other sectarian movements have begun to realize that they will need support from multiple constituencies in order to survive politically. In the likely event that the alliance doesn’t win enough seats to form a government, it can contribute still more profoundly to Iraq’s political development by opting to stay out of power and serve as a parliamentary opposition. Iraq stands at a turning point, where its largely sectarian political movements are experimenting with nonsectarian politics, and where its ruling class is confronting the dead-end to which the spoils system has brought the country. Sadr’s gambit stands a chance, albeit a slim one, of catalyzing the political transformation that Iraq so sorely needs.
To be sure, Iraq will still play host to endemic corruption and patronage, but a sharp change in politics can expand the government’s agenda to include long-term governance along with the usual business of padding state contracts and doling out ghost jobs. Without the sort of transformative nationalist, professional, and anti-corruption politics advocated by Sadr, Iraq is sure to face an ongoing cycle of crises that will destabilize not only Iraq, but also its neighbors and U.S. interests in the Middle East.
A Reckoning Will Come in Syria

A missile is seen crossing over Damascus, Syria April 14, 2018. SANA/Handout via REUTERS[Published in The Atlantic.]
It is undoubtedly a good thing that a small international coalition of the willing responded to Syria’s latest chemical outrage with a limited military strike. But it marks only the first step in an effective strategy to stop Syria’s use of chemical weapons—and more importantly, to hold Russia accountable for its promise to oversee a chemical weapons-free Syria.
Syria and Russia have displayed characteristic bluster and dishonesty, warning of “consequences” for a crisis that the Syrians themselves provoked by apparently violating, once again, their 2013 agreement not to use chemical weapons. Any confrontation with destabilizing bullies is dangerous, and there is no predicting whether and how they’ll respond.
Even a limited and justified effort to contain Syria and its allies carries a risk of escalation. The Trump administration, with its capricious chief executive and broken policy-making process, is ill equipped to forge the sort of complex strategy needed to manage Russia, Syria, Iran, and a Middle East in conflict. Nor has it so far displayed much interest in building the international cooperation necessary to implement such a strategy—although it was a pleasant development that the United States was joined this time by France and the U.K. rather than proceeding unilaterally. However, the considerable drawbacks of the Trump administration don’t give the West a pass when it comes to Syrian use of chemical weapons, and Russia’s belligerent expansionism. Both need to be checked and contained, even considering the additional risks Trump creates.
In order to have any real impact on chemical weapons use, the response needs to be sustained. Every time the regime uses chemical weapons, there needs to be a retaliation, which specifically targets the regime’s chemical-weapons capacity—command and control, delivery mechanisms including aircraft and bases, storage, research, and the like. A political strategy is indispensable as well. Since Russia is the guarantor of the failed 2013 chemical weapons agreement, the West needs to keep Russia on the hook for Syrian President Bashar al-Assad’s use of chemical weapons. The Pentagon chief suggested that these strikes were a one-off, and only time will tell which of Trump’s preferences prevail.
Deft diplomacy will also be necessary to reduce the risks of wider war. It doesn’t help that Trump is undermining the nuclear deal with Iran at the same time as he is ratcheting up the stakes in Syria. One key determinant now is how much Russia is willing to add action to match its relentless campaign of lies and bluster about Syria and chemical weapons. Another is whether Iran, Assad, and Hezbollah are willing to sit on their hands after these strikes. In the past, all three have been willing to refrain from action despite angry promises.
* * *
The problem is the context. Any American action in the Middle East ought to be embedded in a comprehensive, engaged strategy—which is not likely to be forthcoming. Today, we can be sure that America’s significant moves—from proposals to withdraw military assets fighting ISIS in Syria and Iraq, to promises to degrade the capabilities of Bashar al-Assad or limit the reach of Hezbollah or Iran’s Islamic Revolutionary Guard Corps—will land à la carte, increasing the danger of miscalculation and violent, destabilizing escalation.
At stake is how to manage disorder in the Middle East, and more important still, where to draw the line with a resurgent Russia.
Containing rival powers is an art, not a science. Military planners talk about the “escalation ladder” as if it were a chemical equation, but in reality escalation hinges on unpredictable questions of politics, interests, psychology, hard power, and willingness to deploy it.
Obama’s strategy could most simply be understood as a desire to contain regional fires with minimal involvement, while keeping an equal distance from regional antagonists, including Saudi Arabia and Iran, and difficult regional allies including Turkey and Israel. The U.S. got involved in the fight against ISIS, by this logic, with minimal resources and local alliances that it knew couldn’t outlive the immediate counter-terrorism operation.
In the Syrian context, Obama early on made clear that the United States commitment to principles of democracy and human rights would remain primarily rhetorical. Today, the United States has discarded even many of the rhetorical trappings of American exceptionalism. Trump has made clear that he doesn’t apply a moral calculus to superpower behavior. But he’s also expressed personal outrage about Syria’s use of chemical weapons—and he visibly takes umbrage at being personally embarrassed or humiliated.
Whether one thinks it’s wise or fully baked, President Trump also has a Middle East strategy. He wants to reduce America’s footprint, and disown any responsibility for the region’s wars, as if America played no role in starting them and suffers no strategic consequence from their trajectory. He wants to outsource regional security management to regional allies. Most of this is continuous with Obama’s approach, except when it comes to regional alliances; Obama attempted a “pox on both your houses” balance among all of America’s difficult allies. In his biggest departure from his predecessor, Trump has tilted fully to the Saudi Arabian side of the regional dispute, and has erased what little daylight separated American and Israeli priorities in the Middle East.
This is the bedrock of Trump’s moves in the region—moves that are all the more consequential because they are overtly about confronting, or trying to check, Iran and Russia.
* * *
The United States has a critical national interest in reestablishing the chemical weapons taboo. It also has countless other equities in the Middle East that require sustained attention and investment, of diplomatic, economic, and military resources. A short list of the most urgent priorities includes preventing the resurgence of ISIS or its successors; supporting governance in Iraq; limiting the reach and power of militias supported by Iran; and reversing the destabilizing human and international strategic toll of the world’s largest refugee crisis since World War II. A major regional war will only make things worse.
Given the stated priorities of the president, the most realistic possibility is an incomplete, and possibly destabilizing policy of confrontation, containment, and reestablishment of international norms.
But a reckoning can’t be deferred forever. Iran has been surging further and further afield in the Middle East, to great effect. Russia has been testing the West’s limits mercilessly since the invasion of Ukraine and the annexation of Crimea. At some point, the United States and its allies will stand up to this expansionist behavior, although there’s wide latitude about where to set limits. When the West, or some subset of NATO, does confront Russian ambitions, there’s no pat set of rules to keep us safe. Such confrontations are inevitable, and dangerous, and unpredictable. The best we can do is enter into them carefully, with as many strong allies as possible, and clearly stated, limited expectations about what we intend to accomplish.
The United States and its allies also need to more carefully distinguish things they dislike (Iranian influence in Iraq) from things they won’t tolerate (Hezbollah and Iran building permanent military infrastructure in the Golan). Rhetoric in the region often conflates the two. Israeli officials, for instance, talk about “intolerable” developments in Syria, but in practice their security policy often allows for a great deal of ambiguity about just what level of military threat they’re willing to tolerate along their frontiers. Iran, Hezbollah, and now Russia have made grandiose claims about retaliating if the United States takes action, but after past strikes by both the United States and Israel, the actual response has been quite restrained.
The United States and its allies need to set limited, achievable goals. The U.S. might for instance stand firm against the use of chemical weapons, or against new military campaigns against sovereign states, but it can’t very well seek to turn back the clock to a Syria free of Russian and Iranian influence.
In addition, the United States can help the world remember who is the author of this dangerous impasse: Syria, Iran, and Russia, who have serially transgressed the laws of war, lied in international forums, and mocked countless agreements, including the shambolic deal that was supposed to rid Syria of chemical weapons in 2013. This won’t justify American actions or give them political cover, but it is a key reason why we’re in such a difficult position in the first place. Despite American restraint, or even American willingness to tolerate war crimes by Syria and its allies, Syria and its allies have insisted on pushing past every limit and exhausting the world’s willingness to turn a blind eye toward abuses so long as those abuses stay within national boundaries.
Finally, to have any impact at all the United States will need to pay consistent and sustained attention. Russia, Syria, and Iran have gotten away with murder, literally, and have found themselves able to run circles around Western governments that still care to some extent about international norms and institutions. They are dangerous, but they are far weaker than their words would suggest. The West cannot deter every action it does not like, yet it can draw boundaries and impose a cost—but it must do so consistently.
This weekend’s strikes have established a bar and set a perilous, but unavoidable, process in motion. What counts is what comes next.
The Logic of Assad’s Brutality

A child and a man are seen in hospital in the besieged town of Douma, Eastern Ghouta, Damascus, Syria. Picture taken February 25,2018. REUTERS/Bassam Khabieh
[Published in The Atlantic.]
Bashar al-Assad, the president of Syria, might have great contempt for the sanctity of human life, but he is not a reckless strategist. Since 2011, he has prosecuted an uncompromising war against his own population. He has committed many of his most egregious war crimes strategically—sometimes to eliminate civilians who would rather die than live under his rule, sometimes to neuter an international order that occasionally threatens to limit his power, and sometimes, as with his use of chemical weapons, to accomplish both goals at once. When he does wrong, he does it consciously and with intended effect. His crimes are not accidents.
The Syrian regime’s suspected chemical-weapons attack on Saturday in Douma, a suburb of Damascus, suggests that Assad and his allies have accomplished many of their primary war aims, and are now seeking to secure their hegemony in the Levant. But two major factors still complicate Assad’s plans. One is Syria’s population, which to this day includes rebels who will fight to the death and civilians who nonviolently but fundamentally reject his violent, totalitarian rule. The second is President Donald Trump, who has expressed a determination to pull out of Syria entirely, but at the same time has demonstrated a revulsion at Assad’s use of chemical weapons.
Almost precisely one year ago, Assad unleashed chemical weapons against civilians in rural Idlib province, provoking international outrage and a symbolic, but still significant, missile strike ordered by Trump against the airbase from which the attacks were reportedly launched. Assad’s regime was responsible for the attacks and its Russian backers were fully in the know, later evidence suggested, but Damascus and Moscow lied wantonly in their hollow denials.
This weekend, it appears, Assad’s regime struck again. Fighters in Douma refused a one-sided ceasefire agreement, and haven’t buckled despite years of starvation siege warfare and indiscriminate bombing. In what has become a familiar chain of events, the regime groomed public opinion by airing accusations that the rebels might organize a false-flag chemical attack in order to attract international sympathy. An apparent chemical attack followed, killing at least 25 and wounding more than 500, according to unconfirmed reports from rescue workers and the Union of Medical Care and Relief Organizations. The Syrian government and the Russians have once again blamed the rebels, knowing that it will take months before solid evidence emerges, by which point most attention will have turned elsewhere. The pattern is by now predictable. In all likelihood, solid, independent evidence will soon emerge linking the attacks to the Syrian regime.
Assad already has unraveled the global taboo against chemical weapons, in the process exposing the incoherence of the international community. Syria has exposed the international liberal order as a convenient illusion. Western bromides of “never again” meant nothing when a determined dictator with hefty international backers committed crimes against humanity.
Why now? This latest attack in Ghouta, if it holds to the pattern, makes perfect sense in the calculus of Assad, Vladimir Putin, and Iran’s Supreme Leader Ayatollah Ali Khamenei. The successful trio wants first and foremost to subdue the remaining rebels in Syria, with an eye toward the several million people remaining in rebel-held Idlib province. A particularly heinous death for the holdouts in Ghouta, according to this military logic, might discourage the rebels in Idlib from fighting to the bitter end. Equally important, however, is the desire to corral Trump as Syria, Russia, and Iran did his predecessor, Barack Obama.
After the humiliating August 2013 “non-strike event,” when Obama changed his mind about his “red line” and decided not to react to Assad’s use of chemical weapons, the Syrians had America in a box. The White House signed up for a chemical disarmament plan that proved a farce. By the time the agreement had unraveled and Assad was back to using chemical weapons against Syrian citizens, the public no longer cared and Obama was busy discussing his foreign policy legacy.
Trump’s Middle East policy remains a mystery. He has long appeared unconcerned with rising Russian power in the Middle East, but today tweeted that there would be a “big price” for Russia, Iran, and Syria to pay. He seems to prefer a smaller U.S. military footprint, talking repeatedly about pulling troops out of Syria and Iraq. He’s savaged the deal that shelved Iran’s nuclear program, and doesn’t appear impressed by the shabby chemical-weapons agreement in Syria. He doesn’t seem interested in a long-term strategic engagement in the Arab world, but he’s also not interested in propping up the status quo. His reaction to the Khan Sheikhoun attack a year ago aligned with these preferences: He abhorred the attack and spoke with uncharacteristic humanity about the children killed by Assad, and ordered a pointed but limited response. He wasn’t interested in escalating or intervening against Russia or Assad, but he also had no interest in pacifying or reassuring them.
One result of Trump’s confusing Syria policy is that Assad and his backers can’t quite be sure what America is planning—a pullout or a pushback. Hence another chemical attack, which will test the range of America’s response and, perhaps, will paint Trump into the same corner where Obama’s Syria policy languished.
For Assad, there is utility in such a feint, and no real risk. In 2013, he and the rest of the region braced in fear for an expected American response, which was widely expected to jolt the regional state of affairs. Assad has learned his lessons since then. No meaningful American response will be forthcoming, no matter how hideous the war crime. America remains deep in strategic drift, unsure of why it continues to engage in the Middle East, and prone to spasms of hyperactivity rather than sustained attention.
Although we can’t be sure—yet—exactly what happened in Ghouta, we can be confident that it was no accident. Assad is determined to cement his grip once again over Syria, no matter how thoroughly he has to destroy his country in order to restore it. And with Putin’s backing, he is determined to thoroughly discredit what remains of the international community and U.S. leadership. They can’t be sure what Trump will do, but their apparent cavalier use of chemical weapons on the one-year anniversary of the Khan Sheikhoun attacks suggests they’re reasonably confident that the U.S. president won’t take serious action.
This most recent attack, as tragic as it is, is no turning point. It’s more of the same from Assad and his allies, as they solidify the grisly, dangerous norms that they’ve been busy enshrining since 2013.
Managing Syrian Conflict May Be Possible. Resolving It Isn’t.

[Report for The Century Foundation.]
How much, if at all, should the West be involved in Syria as Bashar al-Assad rebuilds the country? The United States and its allies in Europe failed in almost all their policy aims, and the dictator they sought to topple appears to have survived comfortably in power. TCF fellows Thanassis Cambanis and Sam Heller initially set out to write a joint policy recommendation for how the West should approach the conundrums of aid and reconstruction in Syria; but our disagreements proved more instructive than our common ground. What follows is a written dialogue about the Western policy options for dealing with Syria going forward on matters of humanitarian aid, reconstruction, diplomatic relations, and other potential areas of cooperation.
Thanassis Cambanis: Is there any such thing, at this stage, as a good U.S. or Western policy for Syria? This question has been coming up with increasing intensity as the conflict winds down into a final stage. Notwithstanding some arguments that the conflict might drag on for quite a few years, I am convinced that—absent some major game-changing shift—Bashar al-Assad and his allies have won the war. Damascus is now focused on reconquering all of Syrian territory, consolidating its authority, and rebuilding its networks and institutions.
I want us to address a range of questions in this dialogue, including some disagreements between us, about aid, reconstruction, the ethics of engagement with Syria, and the West’s strategic interests in Syria going forward. The recent focus has rightly been on the military imbroglio in northern Syria, which involves Turkey, the United States, and their various Arab and Kurdish proxies. In the long term, however, the West’s most intractable problems have to do with Assad and his government in Damascus.
For the United States and its European partners, this is an ugly and confusing moment. Washington and its hardline anti-Assad allies in Europe seem stuck: they failed to topple Assad, and they don’t want to deal with him. They made strategic commitments in Syria that no longer make sense, but they recognize that Syria is too important for them to try to simply wash their hands of it. Now they have to figure out how to deal with a Syria still under Assad, and still in conflict.
Some of the Western interests at stake in Syria are obvious. Pressing concerns like the Islamic State, or the stabilization of the vast desert zone that stretches between Baghdad and Damascus, require unstinting attention. There are systemic pressures to engage with Assad from many Western quarters, as well. Humanitarians want to distribute aid in regime-controlled Syria, no matter how problematic the regime’s practices of preventing access to civilians considered disloyal. Public and private interests want the West to invest in rebuilding Syria, some for cynical reasons of profit, others for well-meaning reasons of wanting to help the Syrian population that has suffered from a grueling war. Intelligence and security services want to share information with Damascus and engage in joint counterterrorism efforts. Diplomats want to reopen communications channels that were hastily severed during the brief period when many Westerns assumed that Assad was on his way out.
What’s next in a postwar Syria? How do we deal with reconstruction, the aid regime in Damascus, and the more fundamental question of normalization? On what level should the West engage with Damascus at all? At some point, do we resign ourselves to Assad remaining? And what do we do for the Syrian civilians who, through no fault of their own, live under Assad’s rule?
Assad still rules Syria
Sam Heller: Right, these are the big questions policymakers—and anyone who’s vested in this conflict, and in the future of Syria—have to grapple with. And I hope I’m not pulling back the curtain too far here, but we weren’t originally planning to publish this sort of dialogue. We were going to co-author a piece, but it turned out we actually have some big, substantive differences, even as we agree on other key points. After talking it through, we decided it would be more interesting to interrogate those disagreements, rather than write a consensus piece that was brought down to our lowest, least-challenging denominator.
The reality we face is this: Whatever the outcome of this war—and that outcome now seems clearer, day by day—at its end, Syria will not somehow end with it. Syria will continue to exist, as a geopolitical reality, but also as a society and a people.
We need to weigh how to deal with a postwar Syria that is still ruled by Assad, but which is populated by Syrians who have endured years of hardship and death and who are not somehow to blame.
Read the rest of the dialogue at The Century Foundation.
Stop trying to fix everything
[Published in The Boston Globe Ideas.]
INTERNATIONAL PEACE and security is built on rickety compromises. Look around the world at the many places where bitter, deadly conflict has ground to a halt, and you’ll find a series of Rube Goldberg contraptions — fragile, elaborate workarounds, not pat solutions.
The world is a messy place, and foreign affairs magnify human complexity. Americans have long dreamed of simplifying and unifying the world, bringing it in harmony with their values and principles. The impulse is to wade in and resolve things, even if it means breaking up a status quo that functions, with only a vague hope that something better can come of it.
President Trump has renewed interest in upending the world’s status quo. He questioned old chestnuts like the usefulness of NATO, and has reshaped the American approach to Iran, North Korea, and the Palestinians. This year, he dramatically slashed funding to the United Nations agency that since 1948 has been taking care of Palestinian refugees, today numbering in the millions. He has made clear that he’s willing to consider war with Iran. And facing a North Korean leader armed with nuclear missiles, he’s taken a combative approach that scorns the traditional mores of containment.
A close look at some of the most dangerous spots in the world suggests that the United States would do far better if it embraced limbo. Whether the issue is Palestinian refugees, Iran’s nuclear program, or North Korea’s missiles, a messy bad deal is probably the best option. We tend to use the language of avoidance to describe the workarounds that manage long-burning crises — we’re kicking the can down the road, burying our head in the sand, delaying an inevitable moment of reckoning. But what if, in most cases, kicking the can down the road is the only kind of solution that exists, while a more ambitious approach guarantees nothing but more violence and instability?
The North Korea case reminds us just how important these messy deals are for managing the world. The status quo on the peninsula calls into play a bewildering number of governments, interests, and individuals. In the past, the United States has provided aid to North Korea in order to essentially bribe it to slow down its nuclear and missile programs, while China has maintained a tenuous alliance with Pyongyang, on the grounds that it’s wise to keep your friends close and your enemies closer. Kim Jong-Un in a few short years upended this fragile equilibrium and now, once again, world powers are debating how to avoid a nuclear war.
Could we have avoided today’s crisis had world powers been more willing to push for a total solution at some earlier point, 20 or 50 years ago? In fact, the dynamics of international compromise suggest the exact opposite — the more we embrace sloppy status quo deals, the more peace and stability we can enjoy.
* * *
AMERICA, WITH ITS enduring strain of internationalist idealism, imagines itself as a moral knight in a world without values. Other powers are often content to maximize profits in an unjust world order, but Americans like to think their country is willing to forfeit cold interests when they conflict with cherished values. As a result, Washington’s biggest contributions to the world have come from its willingness to radically remake the status quo, supporting a wave of nationalist self-determination a year ago, promoting liberalism and capitalism, and trying to force pragmatic states around the world to adopt certain principles on human rights and trade.
Experience, however, suggests that this quest for solutions is most of the time wrongheaded. Reformers of global politics claim that we face a choice between painful-but-necessary revolutions and untenable jury-rigged compromises in places like the Korean peninsula and the Middle East. But with the exception of rare historical pivot points, the choice is between conflict or tension, on the one hand, and a middling, problematic compromise, on the other. The clean, neat solution is a chimera.
The specific game-changers that Trump appears to be considering from North Korea to the Middle East are alarming, but this approach isn’t new — and the destabilizing results are easily predictable. Presidents Bill Clinton and George W. Bush also believed that America’s exceptional values and economy enabled it to change the way the world functioned. They caused untold damage along the way to figuring out they were wrong.
Clinton believed that after the collapse of the Soviet Union, the remnants of a former superpower would embrace Western ways and American dominance. He missed a historic chance to engage with Russia as a major power, instead trying to transform it into an investment opportunity. Out of that misstep came Putin and another era of conflict between Russia and the West.
George W. Bush took misguided American problem-solving a step further after Sept. 11, causing damage that still reverberates today. After invading Afghanistan, Bush chose to overthrow Saddam Hussein and occupy Iraq, convinced he could remake the Middle East as a model democracy. Bush’s war of choice turned a weakened dictatorship that no longer posed threats beyond its borders into the Iraq we’ve known since 2003 — a deadly place for its own residents and an exporter of instability and extremism.
Iraq is the most striking recent example of what can happen when America tries to fix a cruddy compromise. After the Gulf War of 1991, Saddam Hussein remained in power as a diminished but still awful tyrant. He murdered Kurds, Shiites, and other dissenters. His country declined deeper into poverty and dysfunction. He made unnerving threats. Yet he was kept in check by international sanctions and by an ongoing low-grade war — the “no-fly zone” that protected the autonomous Kurdish enclave in Iraq’s north and quashed any hopes Saddam harbored of reemerging as a regional strongman.
This was a costly and problematic fix. It irritated many of Washington’s allies in the Middle East, and it didn’t fully quiet the fears of Iraq’s neighbors. It left an unjust order in place inside Iraq, thwarting the aspirations of its citizens. It encouraged oil smuggling and international corruption. It kept the United States mired in a perpetual maintenance war.
It was no surprise that many Iraqi dissidents supported the war of 2003. So did some Western humanitarians and democracy promoters. They failed to appreciate just how much worse their solution was than the original problem.
* * *
PARADIGM SHIFTS exert a powerful appeal. We don’t like the way the world works, and imagine that if we’re willing to dream up a completely new approach, we can make the world better. Americans are especially prone to this kind of thinking in foreign affairs, because presidents tend to tune in and then tune out every few years, meaning they bring fresh (and often ignorant) eyes to legacy problems.
Sometimes the results are laudable — like the idea, hatched in the 1990s, that the United States and other powers could sometimes use their militaries to stop genocide.
For the most part, though, the approach is dangerous. Awful status quo compromises might make no sense at first glance, but they’ve usually emerged from struggle and negotiation; they’re not accidents. There’s often no reason to break the logjam and create new (often worse) possibilities.
Magical thinking endangers any meddling power, not just the United States. In Syria’s messy war, it’s Russia (and to a lesser extent Turkey and Iran) that have set unrealistic targets of total control or transformation — and who are now mired in an international proxy war with dangerous risks of escalation.
Trump, egged on by Benjamin Netanyahu’s government in Israel, now appears to believe that squeezing the Palestinian refugee agency will create new opportunities for Arab-Israeli peace talks. Trump also, apparently, hopes to catalyze some change to the limbo of nearly 5.5 million stateless Palestinian refugees who have been living in the Middle East since 1948. On its face, the existing setup seems crazy. World powers set up the United Nations Relief and Works Agency, in 1948 as a temporary salve to the refugee crisis caused by the first Arab-Israeli war. Neighboring Arab countries did not want to integrate Palestinian refuges, for fear that would dilute the refugees’ right to return. Wars and waves of displacement followed. Today’s shaky compromise pleases virtually no one, but provides stability to millions of Palestinians, while reducing the risk of yet another regional war. Closing the relief agency or pressuring Israel’s neighbors might sound like it could prompt bold negotiations — yet it’s all but guaranteed to spur conflict and lead right back to the existing, crummy-but-viable status quo solution.
Of course, there is value in dreaming big. But to achieve big idealistic goals requires a series of small, muddled, and compromised steps. The most unlikely international successes of our time are deeply flawed, and came about through a series of profoundly unsatisfying, compromised stages. The United Nations failed to stop all wars, yet it has undeniably made the world a significantly less deadly and more stable place, even though it has been party to the profoundly compromised ways of international deal making. The European Union stemmed from a similar stream of compromises: The biggest and most successful experiment in world history of people voluntarily uniting and sharing power, the EU has faced justifiable accusations of being insufficiently democratic at each stage .
In the messy and deadly arena of world politics, workarounds aren’t always great outcomes. Most of the time, however, they’re the best alternative. Fix them at your peril.
Saudi Arabia’s Dangerous Gamble

[Published in The Boston Globe Ideas.]
FOR ITS ENTIRE modern existence — nearly 90 years — the kingdom of Saudi Arabia has wielded outsize influence over the rest of the world because of the wealth afforded by its bottomless oil reserves and its special status as the home of Islam’s holiest sites. The House of Saud, its absolute rulers, has defined itself by a rigid alliance with Islamic fundamentalists and a reactionary aversion to any change in the status quo.
That’s why the country’s recent swirl of activity has confounded observers. The kingdom’s de facto ruler, Crown Prince Mohammed bin Salman, 32, has agitated for a regional war, locked up rival princes, and tossed aside political conventions. At the same time, he swept up the line of succession with dizzying speed, consolidating power in a narrow circle.
But it would be a mistake to believe that Mohammed bin Salman is a reformer, as many US government officials and professional analysts apparently do. There’s only one thing he’s proven interested in reforming, and that’s his family’s undiluted and absolute grip on power — which is no small thing. The young prince might succeed in his effort to refashion the Saudi monarchy. But his wider plans for his country, the Middle East, and Islam have very little chance of success because of Saudi Arabia’s structural limitations and because the supposed reformer himself is an authoritarian — an unaccountable hereditary monarch whose own legitimacy could not survive serious modernization.
Despite its frozen-in-amber culture, Saudi Arabia has pivotally shaped its closest ally, the United States. Its colossal sovereign wealth finances US debt; it can regulate world oil markets to suit Washington’s interests, as it did during the invasion of Iraq; and its ultra-radical state-sponsored brand of Islam has been a central driving force in the rise of violent extremism for nearly 40 years (critics of the kingdom habitually point out that 15 of the 19 hijackers on 9/11 came from Saudi Arabia). For as different as the two nations are, their fates and fortunes are often intertwined.
Which is why Washington is paying close attention to the regional blowback provoked by Saudi Arabia’s departure from its old gradualist approach. The kingdom broke with its historic, if mostly rhetorical, commitment to a Palestinian state when it voiced only pro forma objections to President Donald Trump’s recognition of Jerusalem as Israel’s capital. Palestinian leaders increasingly see Saudi Arabia as an ally of Israel.
In early December, Saudi Arabia tried to salvage its disastrous war in Yemen with a surprise rapprochement with Ali Abdullah Saleh, the former president and ally, who had been fighting against Riyadh for the last three years. The new alignment lasted all of two days, until Saleh was murdered. Saleh and the Saudis had once again underestimated the power of their Iranian-backed rivals, the Houthis.
And in one of its most brazen recent failures, Mohammed bin Salman tried unsuccessfully in November to unseat Lebanon’s prime minister (a Saudi loyalist) and replace him with a more slavish apparatchik. That sowed fears of a new regional war, involving Iran, Israel, Hezbollah, and Saudi Arabia. The gambit quickly sputtered into failure.
Jerusalem is primarily a Trump move, and the war in Yemen involves security concerns that stretch to the early days of the Saudi monarchy. But the Lebanon crisis involves well-known regional politics and represents a completely voluntary own-goal. How mighty Saudi Arabia’s effort to bully little Lebanon fizzled says a lot about what the Saudis seem to be after — and why they’re unlikely to get it.
Mohammed bin Salman’s emerging leadership is already turning into a study in the limits of assertiveness on the global stage. Saudi Arabia has gained a brash leader intent on throwing his country’s weight around, but he’s unwittingly made it clear that money only goes so far — and that the Saudi political system may be fundamentally unreformable.

SAUDI ARABIA’S LEADERS are unfathomably rich and, contrary to some simplistic depictions, do follow a grand strategy in matters of religion, regional politics, oil markets, and finance. They’re not rubes, and possess serious capacity to affect the world. Among other achievements, the Saudis have forged an enduring alliance with the United States, and have managed their public relations better than most autocratic states.
The American narrative about Saudi Arabia has always skirted wide of reality. Ever since FDR, the United States has relied on the kingdom — initially for its oil, later for its willingness to manage global oil supply in line with American policy objectives. As a result, there has been a steady appetite for stories about Saudi reform, which ring hollow over time. Abdullah Al-Arian, a Georgetown historian, compiled 70 years of clips from The New York Times that “describe Saudi royals in the language of reform,” starting with a 1953 article that describes King Saud as “more progressive and international-minded than his autocratic father,” and ending with a Thomas Friedman column from November entitled “Saudi Arabia’s Arab Spring, at last.” Western narratives focus on reform, real or imagined, as the United States pursues cooperation on energy and security — and as a result, Al-Arian said, the United States often misses troubling realities, like the repression of Saudi citizens, or the plummeting of America’s reputation in the region. “It would seem to result in poor policy choices,” he said.
On the other hand, the Saudis have been neither sophisticated nor realistic about setting goals, suffering from the misplaced conviction that their wealth and custodianship of the birthplace of the prophet Mohammed, the most holy site in Islam, could translate into control of the wider Islamic world.
Mohammed bin Salman rose to power when he father took over as king nearly three years ago. He took over key positions, including the defense ministry, and pushed for a war in Yemen over the objections of older royals. This year, the previous crown prince was unceremoniously deposed and replaced with bin Salman. No one in Saudi Arabia pretends that the father is making the decisions; the younger bin Salman is openly in charge. (Foreigners often refer to the regent by his initials, MbS.)
After decades of snoozing through regional affairs, Saudi Arabia has been playing catchup. When uprisings against Arab despots broke out in 2010 and 2011, Saudi Arabia’s monarchs understood any popular, mass politics (whether secular or Islamist) posed a threat to their anachronistic form of rule by divine right. They rallied with uncharacteristic vigor against the political energy that the uprisings unleashed. They dispatched troops to Bahrain to crush a political rebellion by the Shia majority. They spent billions backing a secular military coup in Egypt, while simultaneously pouring weapons and money into jihadist rebels in Syria. They’ve backed one warlord in Libya’s civil war. They’ve cracked down hard on the Muslim Brotherhood region-wide, and have tried to assert control over Palestinian factions.
The Saudis embarked on this mad rush only after they realized just how deeply their regional influence had eroded. Iraq, once a reliable linchpin of the Sunni Arab regional bloc, is now governed mostly by its Shia majority, and enjoys friendly relations with Iran. Lebanon has slipped out of Saudi’s orbit and closer to Iran, despite billions of dollars invested over the course of half a century to cultivate loyalty. Once-reliable allies have spurned the Saudi agenda even while accepting money, or have switched sides entirely.
It’s not clear, still, whether the Saudis understand their own unpopularity.
As the monarchy dreams of pushing back Iran and asserting itself as a new regional hegemon, it should study the lessons of its sharpest recent failures: Yemen, Lebanon, and their own royal purge marketed as a corruption crackdown. Saudi Arabia is unlikely to transform into a republic anytime soon. With its massive oil reserves and complete dependence on foreign non-citizen labor to make its economy function from top to bottom, it’s unlikely to create a modern economy despite the crisp assertions authored by the foreign management consultants who wrote Vision 2030, Mohammed bin Salman’s blueprint for the future.

OF COURSE, SAUDI’S EPIC, bungled attempt to change Lebanon’s political order made compelling drama: the sovereign head of a state summoned to Saudi, forced to resign, then detained against his will. During the same weekend, Mohammed bin Salman arrested all the rich or powerful royals not completely loyal to him. Some were held in a luxury hotel, and few reportedly died in suspicious circumstances. He summoned the Palestinian leader and apparently tried to give him marching orders as well. He ordered an emergency summit of the Arab League. He issued a script for Egypt, which despite its reliance on Saudi money still wields significant political influence in the Arab world.
Here was a turbo-charged leader making the case for the great-man theory of history, reordering an entire region by force of will — in dramatic fashion and in the public eye. It was riveting drama because the stakes were high.
Very quickly, the monarch found himself hitting the structural limits on Saudi power. Egypt’s dictator pushed for the immediate release of Lebanese Prime Minister Saad Hariri. Instead of taking the bait, Hezbollah dismissed Hariri’s coerced resignation. There wouldn’t be saber rattling and threats of war, Hezbollah said; it would keep calm and wait to talk to Hariri in person when he was free to come home.
Saudi expected Lebanon’s Sunni community to rally for confrontation with Iran and Hezbollah, even if Lebanon burned in the process. But with their leader kidnapped, Lebanese unsurprisingly turned against the responsible party — Saudi Arabia. “The Lebanese are not a herd of sheep or a plot of land whose ownership can be transferred from one person to another,” declared Lebanon’s interior minister, Nohad Machnouk. “Lebanon’s democratic system is based on elections, not on a simple pledge of allegiance.”
The Saudi king had put the Middle East on notice that he expected his beneficiaries, especially Sunni Arab leaders, to do his bidding. To his surprise, they refused. The president of France, according to diplomatic sources, flew to Riyadh to explain to the young prince that Saudi Arabia wasn’t the only powerful nation with equities in Lebanon — and that even imperial meddling has rules and limits. Mohammed bin Salman was apparently baffled that he couldn’t simply fire the prime minister of another sovereign nation.
Egypt might have prepared Mohammed bin Salman for the complexities of dealing with weak but sovereign states. It was Saudi intervention that helped Abdel Fattah el-Sisi seize power in Egypt, and Saudi money that ensured his survival. Sisi was willing to make the controversial decision to sign over the strategic Red Sea islands of Tiran and Sanafir to Saudi Arabia. But on many other key issues he has defied Saudi orders. He refused to send Egyptian troops to Yemen, broke ranks by maintaining relations with Syrian President Bashar al-Assad, and came down on Lebanon’s side during the Hariri crisis. He openly opposes provoking a regional war with Iran. His attitude toward Saudi was clear in leaked tapes where he told his chief of staff that he could do whatever he wanted while still hitting up Saudi for more cash: “They have money like rice, man!”
In the latest crisis, a further humiliation came from Israel. Saudi’s supporters spread rumors through diplomatic and media channels that a new war was imminent, between Israel and Hezbollah. Hezbollah’s leader had already announced his disinterest in a conflict at the present time. Israel followed suit, in an unprecedented interview by the Israeli military’s chief of staff with the Saudi news site Elaph. In the interview, Gadi Eisenkot praised the Saudi leadership’s anti-Iran stance, and offered deeper intelligence cooperation — a marked change from the days when Saudi Arabia backed the Palestinian side. More importantly, though, Eisenkot emphasized the line already propagated in the Israeli press, that Israel wouldn’t start a war on Saudi’s behalf. “We have no intention of attacking Hezbollah in Lebanon and bring about a war,” he said.

STUCK IN THE MIDDLE of therough and tumble of Middle East politics, Mohammed bin Salman was receiving a real-time education in realpolitik. The situation on the home front wasn’t unfolding according to plan either.
Rival royals were rounded up in a lightning overnight purge. Many of the detained billionaires are, by all accounts, genuinely corrupt; the problem is that the sweep was undertaken arbitrarily. Saudi’s modernization plans depend on foreign investment and a credible approximation of rule of law. Bin Salman primarily cares about his power base, but his future depends on economic viability. He might only care rhetorically about his proposals to change his country’s culture and religious practice, but he definitely wants to preserve his kingdom’s wealth. The Saudi economy needs to diversify — but foreign governments and global capital will be wary of deal-making with a capricious, unaccountable, and flamboyant head of state who can’t even be counted upon to be consistent in the corruption he’ll tolerate.
Many of the detained royals are now negotiating for their freedom. The anti-corruption crackdown turns out to be a shakedown in country where corruption is everything. Mohammed bin Salman, the prince with the half-billion dollar yacht claims to be cleaning house by confiscating the assets of his cousins. They might well deserve it, but nothing in this process makes clear why. Nor does it provide any comfort to those who worry that this endemic graft indirectly threatens world finance and oil markets, in which the Saudi royal family plays an outsize role.
One reason why the Saudis get the benefit of the doubt is good press, for which they pay top dollar. After he was first appointed deputy crown prince in April 2015, bin Salman met with foreign politicians and granted long interviews with journalists. By the time he engineered a quasi-coup against rival branches of the royal family, bin Salman had cornered the narrative. He was portrayed as a young energetic reformer. Rumors quickly made it into the mainstream media that his unceremoniously deposed uncle was addicted to opiates. Meanwhile, bin Salman suffered little critical press about the disastrous war he started in Yemen, or about his superyachts, or his $450 million purchase of a Leonardo da Vinci painting this month in the middle of his austerity program.
Rhetoric eventually has to square with reality. Bin Salman will have to learn to navigate a world in which he is an important, but not omnipotent player. Saudi wealth and oil will almost always assure it a hearing, and its historical alliance with the United States endows it with extra clout. But its reach is limited. Few states admire Saudi Arabia’s opaque and personalized form of authoritarianism. The most important countries in the region tend to be republics, even those ruled by military despots or theocrats. For all its wealth, Saudi Arabia has underperformed. Its military can’t project power outside its borders, and the money it spends abroad on proxy-building tends to bring little return and less loyalty.
Meanwhile, its biggest regional rival, Iran, has managed to consolidate influence across the region. Saudi Arabia is a middle-rank power with few levers at its disposal. Its most successful leaders have tried to maneuver within the zone of the possible, understanding where Saudi Arabia could use moral, religious or sectarian suasion to its advantage, and where it could get away with some coercion. Mohammed bin Salman has grossly overestimated his reach. For nearly three years, his military campaign in Yemen has achieved none of its strategic goals, while inflicting shocking levels of human misery. Instead of revising his ambitions, he’s aimed still higher. His present season of overreach and humiliation suggest, once again, that it’s time for the young king-in-waiting to align his goals with reality. As long as he doesn’t, an unsettled region — and, ultimately, the rest of the world — can expect to continue paying the price.
Hariri’s Unnerving Interview
Lebanon’s Prime Minister Saad al-Hariri, who has resigned, is seen during Future television interview, in a coffee shop in Beirut, Lebanon November 12, 2017. Photo: REUTERS/Jamal Saidi
[Published in The Atlantic.]
In the Middle East, the parlor game of the moment is guessing whether Saad Hariri, Lebanon’s prime minister—or is it ex-prime minister?—is literally, or only figuratively, a prisoner of his Saudi patrons. In a stiff interview from an undisclosed location in Riyadh on Sunday, Hariri did little to allay concerns that he’s being held hostage by a foreign power that is now writing his speeches and seeking to use him to ignite a regional war. He insisted he was “free,” and would soon return to Lebanon. He said he wanted calm to prevail in any dispute with Hezbollah, the most influential party serving in his country’s government.
Since Hariri was summoned to Saudi Arabia last week and more or less disappeared from public life as a free head of state, rumors have swirled about his fate. On November 4, he delivered a stilted, forced-sounding resignation speech from Riyadh. Michael Aoun, Lebanon’s president, refused to accept the resignation, and Hezbollah—the target of the vituperative rhetoric in Hariri’s speech—deftly chose to stand above the fray, absolving Hariri of words that Hezbollah (and many others) believe were written by Hariri’s Saudi captors.
The bizarre quality of all this aside, the underlying matter is deadly serious. Saudi Arabia has embarked on another exponential escalation, one that may well sacrifice Lebanon as part of its reckless bid to confront Iran.
Foreign influence seeps through Middle Eastern politics, nowhere more endemically than Lebanon. Spies, militias, and heads of state, issue political directives and oversee military battles. Foreign powers have played malignant, pivotal roles in every conflict zone, from Iraq and Syria to Yemen and Libya. Lebanon, sadly, could come next. Even by the low standards of recent history, the saga of this past week beggars the imagination, unfolding with the imperial flair of colonial times—but with all the short-sighted recklessness that has characterized the missteps of the region’s declining powers.
Saudi Arabia, it seems, is bent on exacting a price from its rival Iran for its recent string of foreign-policy triumphs. Israel and the United States appear ready to strike a belligerent pose, one that leaders in the three countries, according to some reports, hope will contain Iran’s expansionism and produce a new alignment connecting President Donald Trump, Saudi Crown Prince Mohammed bin Salman, and Benjamin Netanyahu.
The problems with this approach are legion—most notably, it simply cannot work. Iran’s strength gives it a deterrence ability that makes preemptive war an even greater folly than it was a decade ago. No military barrage can “erase” Hezbollah, as some Israel war planners imagine; no “rollback,” as dreamed up by advisers to Trump and Mohamed bin Salman, can shift the strategic alliance connecting Iran with Iraq, Syria, and much of Lebanon.
Saudi Arabia, as the morbid joke circulating Beirut would have it, is ready to fight Iran to the last Lebanese. But the joke only gets it half right—the new war reportedly being contemplated wouldn’t actually hurt Iran. Instead, it would renew Hezbollah’s legitimacy and extend its strategic reach even if it caused untold suffering for countless Lebanese. Just as important, a new war might be biblical in its fire and fury, as the bombast of recent Israeli presentations suggests. But that fire and fury would point in many directions. Iran’s friends wouldn’t be the only ones to be singed.
Saudi Arabia’s moves have gotten plenty of attention in the days since Mohamed bin Salman rounded up his remaining rivals, supposedly as part of an anti-corruption campaign. Hariri was caught in the Saudi dragnet around the same time. It seemed puzzling at first: For years, Saudi Arabia had been angry with Hariri and his Future Movement, its client in Lebanon, for sharing power with Hezbollah rather than going to war with it. Riyadh was clearly displeased with Hariri’s pragmatic positions. He had learned the hard way, after several bruising political battles and a brief street battle in May 2008, that Hezbollah’s side was the stronger one. Rather than fuel a futile internecine struggle, Hariri (like the rest of Lebanon’s warlords) opted for precarious coexistence.
Once it became clear that Hariri could do nothing to prevent Hezbollah’s decisive intervention in the Syrian civil war, Saudi Arabia cut off funding for Hariri, bankrupting his family’s billion-dollar Saudi construction empire. It also ended its financial support for the Lebanese army, cultivating the impression that it considered Lebanon lost to the Iranians and Hezbollah.
Now, Saudi Arabia has steamed back into the Lebanese theater with a vengeance. It dismisses Hezbollah as nothing but an Iranian proxy, and, in the words uttered by Hariri in his resignation speech, wants to “cut off the hands that are reaching for it.” In what must be an intentional move, it has destroyed Hariri as a viable ally, reducing him to a weak appendage of his sponsors, unable to move without the kingdom’s permission. Mohamed bin Salman won’t even let him resign on his home soil. If Hariri really were free to come and go, as he insisted so woodenly in his Sunday night interview, then he would already be in Beirut. Even his close allies have trouble believing that threats against his life prevent him from coming home, and the Internal Security Forces, considered loyal to Hariri, denied knowledge of any assassination plot.
The Saudis have fanned the flames of war, seemingly in ignorance of the fact that Iran can only be countered through long-term strategic alliances, the building of capable local proxies and allies, and a wider regional alliance built on shared interests, values, and short-term goals. What Saudi Arabia seems to prefer is a military response to a strategic shift, an approach made worse by its gross misread of reality. In Yemen, the Saudis insisted on treating the Houthi rebels as Iranian tools rather than as an indigenous force, initiating a doomed war of eradication. The horrific result has implicated Saudi Arabia and its allies, including the United States, in an array of war crimes against the Yemenis.
Hariri has clearly tried to balance between two masters: his Saudi bosses, who insist that he confront Hezbollah, and his own political interest in a stable Lebanon. On Sunday night, he appeared uncomfortable. At times, he and his interviewer, from his own television station, looked to handlers off camera. The exchange ended abruptly, after Hariri implied that he might take back his resignation and negotiate with Hezbollah, seemingly veering from the hardline Saudi script. “I am not against Hezbollah as a political party, but that doesn’t mean we allow it to destroy Lebanon,” he said. His resignation does nothing to thwart Hezbollah’s power; if anything, a vacuum benefits Hezbollah, which doesn’t need the Lebanese state to bolster its power or legitimacy.
One theory is that the Saudis removed Hariri to pave their way for an attack on Lebanon. Without the cover of a coalition government, the warmongering argument goes, Israel would be able to launch an attack, with the pretext of Hezbollah’s expanded armaments and operations in areas such as the Golan Heights and the Qalamoun Mountains from which they can challenge Israel. Supposedly, according to some analysts and politicians who have met with regional leaders, there’s a plan to punish Iran and cut Hezbollah down to size. Israel would lead the way with full support from Saudi Arabia and the United States.
Short of seeking actual war, Saudi Arabia has, at a minimum, backed a campaign to fuel the idea that war is always possible. But such a war between Saudi Arabia and Iran would upend still more lives in a part of the world where the recently displaced number in the millions, the dead in the hundreds of thousands, and where epidemics of disease and malnutrition strike with depressing regularity. Short of direct war, Riyadh’s machinations will likely produce a destabilizing proxy war.
If Hariri were a savvier politician, he could have used different words; he could have refused to resign, or insisted on doing so from Beirut. But he is an ineffective leader in eclipse, unable to deliver either as a sectarian demagogue or a bridge-building conciliator. Saudi Arabia’s plan to use him to strike against Iran will fail. Just look at how willfully it has misused and now destroyed its billion-dollar Lebanese asset. It’s a poor preview of things to come in the Saudi campaign against Iran.
Iraq after Kurdistan and Mosul
With Kurdistan’s independence referendum ending in fiasco, and Mosul recaptured from ISIS, what’s next for Iraq? Arguably, Iraq is the biggest success story right now in the Arab world.
In the latest episode of the TCF World podcast, I asked two experts to share their views on what comes next for federalism and the reconstitution of an Iraqi state and identity. You can listen to Christine van den Toorn and Renad Mansour through TCF’s website, or you can find the podcast directly on iTunes.
Lebanon not just blank slate
A recent workshop at LAU, in which I took part, looked at Lebanon’s role in the Arab uprisings, as a force and actor and not merely as a blank slate. This kind of research is critical, especially since Lebanon has long been on the cutting edge of (often malign) political experiments and trends. The more research and reporting on Lebanon, the better we’ll understand the forces at play here and in the regional neighborhood. The participants shared some useful work that ought to help, in the long run, further our understanding of Lebanon’s role in the region, and put paid to the Lebanese exceptionalist perspective that holds that Lebanon unfolds somehow in isolation from its region.
TCF foreign policy podcasts online
After some experimentation over the summer, TCF has finally — officially — launched its foreign policy podcast channel. You can subscribe on iTunes or Podbean.
The first four episodes are up, including a conversation with Lina Attalah about press freedom in Egypt, some thought about Hezbollah and Iran, ISIS, and the next stage in Syria.
Podbean Channel: https://thecenturyfoundation.podbean.com/
iTunes Channel: https://itunes.apple.com/us/podcast/id1295785057
Iran’s Edge
Iran’s Revolutionary Guard Corps in a military parade marking the 36th anniversary of Iraq’s 1980 invasion of Iran, in front of the shrine of late revolutionary founder Ayatollah Khomeini, just outside Tehran, on Sept. 21, 2016. AP PHOTO/EBRAHIM NOROOZI
[Originally published in The Boston Globe Ideas section.]
The decision by President Trump to decertify the Iran deal and impose sanctions on the Islamic Revolutionary Guard Corps marks the public debut of a campaign that’s been underway since the spring, when Trump ordered his national security team to find ways to “roll back” Iranian influence.
As we’re likely to see over the coming year, Iran has cultivated its own options to throw nails and bomblets in the path of any presumptive American juggernaut. It might be possible to roll back Iran’s reach in the Middle East, but not without painful costs, which can be visited on a web of American targets and allies located throughout Iran’s sphere of influence.
According to Middle East experts who have consulted privately for the administration on Iran policy, the president asked for ways to raise the price for Iran of its expansionist policy in the region — without exposing America to direct new threats. That might not be possible.
After a decade during which America tried to balance the regional contest between Iran and Saudi Arabia, with its deepening Shia-Sunni sectarian inflection, Trump has cast his lot with one side. When he placed his hands on a glowing orb in Saudi Arabia, he overtly endorsed an all-Sunni gathering whose primary purpose was to counter Iran in the region.
We’re about to witness a real-life test of an Iran policy that eschews diplomacy and embraces confrontation. Trump and his advisers have described their volte-face against Iran in terms of deterrence theory, which attempts to put a scientific gloss on how threats of war play out between two nuclear powers capable of mutually-assured destruction.
But it’s not deterrence theory that offers the best guess of what the coming escalation with Iran might look like, it’s the gritty modern historical record.
During America’s messy occupation of Iraq, militias trained and funded by Iran were able to pose the most sustained military challenge to US troops. Sophisticated bombs called “explosively-formed penetrators” were able kill Americans even in the US military’s best armored vehicles. US officials believed that Iran provided these weapons and the training to use them — but kept their hands off the operations so they wouldn’t provoke a direct conflict.
Late in his final term, in 2007, President George W. Bush slapped a foreign terrorist organization designation on the elite Quds Force of the Iranian Revolutionary Guard, but stopped short of designating the entire armed forces, a move which Iranian leaders have said they would consider an act of war. Around that same time, some American officials were musing publicly about preemptive military strikes on Tehran’s nuclear program.
Then, as now, Washington was exploring a wider escalation with Iran while also probing for ways to prick Iran in regional flashpoints. One apparent pushback saw American troops detain five Iranian employees at the consulate in the Iraqi city of Erbil.
In that heated context, a remarkable raid took place on January 20, 2007. Militiamen in American uniforms, driving a convoy of SUVs identical to those commonly used by US troops and contractors, sped into an American facility in Karbala. They were inside before guards noticed anything amiss. They spared the Iraqis on the base, targeting only Americans, and managed to kidnap five soldiers who were later killed by their captors.
Evidence later emerged connecting the attack to Iran; not conclusively enough to justify direct retaliation by the United States, but enough to leave another bruise, and another argument that America couldn’t tangle with Iran cost-free.
Officials and analysts around the Middle East have speculated for years about where Iran might begin striking back against American interests if the two nations came to blows.
The Karbala raid suggests what Iran is capable of. In recent statements, commanders of the IRGC have warned that American installations could be targeted anywhere within 1,250 miles of Iran’s borders — the range of Tehran’s conventional missiles.
But a direct strike would engulf Iran in a direct war with the United States in which it would be at a great disadvantage. History suggests that Iran’s leadership prefers indirect conflict, with all the advantages of asymmetric warfare and plausible deniability. And there are a plethora of American targets in the Middle East that are exposed to Iranian-linked malefactors who could strike with weapons much more basic, and less traceable, than a long-range missile.
Today there are more than 5,000 American troops stationed in Iraq. Meanwhile, Iran’s regional relationships have grown deeper and broader. Along with its long-time militia allies, including foreign groups whose members spent the 1980s and 1990s in exile in Iran, today there are tens of thousands of new militiamen actively trained and advised by Iran. They are part of the Popular Mobilization Forces created to fight the Islamic State, or ISIS. Many PMF units are directly under Iran’s control but fought hand in glove with the United States in the campaign against ISIS.
Today, some of those same PMF militia fighters are embroiled in a dangerous confrontation with Kurdish Peshmerga forces around Kirkuk.
A quick perusal of Iran’s reach and alliances lends credence to what longtime Iran watchers argued: Iran does best in a regional proxy war. According to this analysis, Iran has little incentive to break out to a nuclear weapon, or fire the long-range rockets it already has developed, while it has every incentive to magnify its ability to destabilize and threaten rivals with indirect attacks by groups it supports: acts of sabotage, terrorism, and proxy warfare. (Supporters of the Iran nuclear deal argued that Iran’s penchant for indirect warfare meant it was never likely to pose a nuclear threat even if it did acquire a weapon, while critics said it underscored the destabilizing danger of Iran’s unchecked spoiler tactics.)
Examples abound, from the campaign of hostage-taking in Beirut in 1980s (mostly conducted by Hezbollah, but clearly at Iran’s direction), to the creation of proxies in Lebanon, Syria, and Iraq, to support for hyper-sectarian politics across the Levant and the Arabian peninsula. Sure, other regional powers like Saudi Arabia have used the same tactics, but to far less effect and usually not in direct opposition to US interests (at least when it comes to state-orchestrated violence; terrorist blowback and a permissive environment for terrorism are another matter entirely, and the reason why a sounder policy from Washington would entail containing Saudi Arabia as well as Iran.)
Status quo powers like the United States, Russia, and China, even when they are competing for influence, share a common interest in unified, effective state structures. They like to do deals (for oil, weapons, or other commodities) and build alliances with unitary governments that have a clear leader and functional institutions.
Iran, by contrast, has done well in the Middle East when its neighbors are too weak and fragmented to pose a threat. The Islamic Revolution almost collapsed during the war with Saddam Hussein in the 1980s. Iran’s leaders concluded that their best bet was to cultivate unstable, fragmented, and squabbling neighbors who couldn’t pose such a threat. Iran has mastered better than any other intervening power the tactics of jockeying for influence in a kaleidoscopic, unstable war zone with dozens of competing militias and power centers.
While other powers have struggled to maintain toeholds in shifting environments like Iraq, Syria, and Lebanon, the security apparatus of Iran has built thriving spheres of influence; its operatives are comfortable working with multiple, even dozens, of proxies, warlords, and local allies. The Iranians are able to hedge their bets and extend their influence in these fragmented zones of authority not because they are evil geniuses, but because their goals are different and easier to achieve.
Furthermore, the Iranians have a home-court advantage – their stake in the Middle East can’t fluctuate like it does for faraway imperial powers. Tehran also has invested in a long game, without end. Many of its operatives spend their entire careers working in Iraq, Syria, or Lebanon; they speak fluent Arabic and build relationships over decades with their military, intelligence, and political counterparts.
They seek unimpeded military access to proxies, influence with governments, and access to markets — all goals easily achieved in a context of fraying state authority.
Needless to say, it’s easier to undermine and erode state institutions than to build them.
This skill set — honed in Lebanon since the early 1980s and then later in Syria and Iraq — translated easily to the war in Yemen that expanded two years ago. It most certainly will help Iran in a phase of renewed confrontation with Trump’s America.
The War on ISIS distracted from Middle East fragmentation
Fighters of the Syrian Democratic Forces make the V-sign as their convoy passes in Ain Issa, Syria, on October 16, 2017. Photo: Erik de Castro / Reuters
The fall of the Islamic State’s stronghold and symbolic capital in Raqqa brings a certain grim satisfaction. It was in this regional riverbank city that the grisly, nihilistic group honed its medieval methods, spreading terror with acts of violence both intimate and public. A coalition consisting of Kurds, the U.S. military, and a supporting phalanx of Syrian-Arab militias, apparently drove the last ISIS holdouts from Raqqa on Tuesday. No longer will ISIS plant severed heads on stakes in the main town square and spew hate from repurposed churches and government buildings, painted black.
But let’s not kid ourselves. The end of ISIS’s temporal empire and first capital does nothing to spare the Middle East and the world of the array of strategic threats and headaches of which jihadis are but one leading edge. At best, the war against ISIS pressed a “pause” button on the unspooling narrative of conflict and fragmentation. With the fall of Raqqa, the sad story will pick up exactly where it left off in 2014.
Just before ISIS rose from fringe extremist group to the world’s leading transnational, violent proto-state, the Middle East was riven by destabilizing conflicts that threatened to blow the already-teetering region apart. Syria and Iraq were imploding as states, with shrinking state authority leaving terrorist and extremist groups ever more freedom to organize and launch attacks in the spiraling ungoverned zones of the Levant. America had disinvested and none of the would-be replacement powers in the region demonstrated the capacity for stability, control, or governance.
The ISIS horror show spread from Raqqa in January 2014 to Mosul in June of that year. Briefly, the group seemed able to strike everywhere, from Marseilles, Paris, and Brussels, to Baghdad and Tehran. For an instant, that threat spurred a clarity of focus.
Briefly united by common cause against ISIS, odd bedfellows temporarily set aside their differences. Although they didn’t always coordinate directly, almost every significant entity in Syria and Iraq supported the anti-ISIS campaign. Kurdish factions that detested each other worked in sync against ISIS. So did Baghdad and Iraqi Kurdistan, Damascus and many of its sworn opponents, and Iran and the United States. But every single one of the destabilizing conflicts that was flaring in 2014 is worse today.
The United States, along with leaders in the Middle East, wasted the opportunity to build on the temporary anti-ISIS wartime alliance to address deeper conflicts. They did not begin laying the foundations for reunified states that elicited loyalty from disenfranchised populations, like Kurds and Sunnis. Instead, they ignored all the festering divisions, and, in many cases, made them worse. In Iraq, the United States emboldened a corrupt and ineffectual Kurdish leadership, which had let its peshmerga fighters fall into an alarming state of disarray. It rearmed the Iraqi military as well, aware that both the Kurds and Baghdad were likely, at a later stage, to aim at one other the weapons they were given to fight ISIS. Kirkuk is just one harbinger of the post-ISIS struggle, which is likely to break out with renewed fury like a cancer surging back after remission.
Just as the dispute between Iraqi Kurds and Baghdad simmered in the background while everyone’s eyes were on ISIS, so did the same Sunni and tribal grievances fester in the deserts of Syria and Iraq. Jihadi violence will continue its cyclical rise and fall in Iraq, as it has without fail since the Iraqi state was destroyed in the American invasion of 2003. Until Iraq is a fully governed and secured nation, extremist groups will continue to thrive in its margins and seams.
More consequential are the sectarian fissures. Baghdad seems, sadly, on track to continue to treat Sunni Arab citizens as second-class citizens and suspected fifth-columnists. Although Iraqi Sunnis shoulder some of the blame for refusing to commit to an Iraqi state that they no longer dominate, it is the government in Baghdad, with its Shia sectarian overtones, that is primarilyresponsible for sharing power with Sunni citizens, and with tribes.
In Syria, Bashar al-Assad’s regime also seems to believe that it can indefinitely exclude or diminish entire swathes of it population. There, America has also added new problems through its troubled alliance with the country’s Kurds. Casting about for an effective proxy militia in Syria, the U.S. military finally found the Syrian Democratic Forces (SDF)—really a shell for Kurdish militants affiliated with the Kurdistan Workers Party (PKK). This Kurdish-dominated militia proved able, or at least willing, to act as a conduit for American military aid and interests. But the PKK tops Turkey’s enemies list, and despite its nation-building rhetoric, is seen as a vehicle of Kurdish ethnic interests at odds with the Arab population. Predictably, America’s marriage of convenience with Syrian Kurds has driven a wedge between America and Turkey and sowed mistrust among Syrian Arabs.
The Kurds in Iraq ignored U.S. advice as well. Washington warned them against holding their independence referendum. It made clear that the Kurds wouldn’t be able to take Kirkuk, and that without Kirkuk’s oil and Turkey’s support, their independent state wasn’t viable.
For the first time in years, Washington at least emerged in the Kirkuk crisis on the side of national unity and the Arab state. Kurds might feel justifiably betrayed, but the U.S. decision not to back Kurdish aspirations vindicates the view that the United States isn’t secretly agitating to break the Middle East into a patchwork of feuding statelets.
After ISIS, the core problem is state collapse and unaddressed minority grievances. As goes Iraq, so goes Syria: If it doesn’t want to end up as a volatile confederation of sectarian mafia-warlords like Lebanon—but deadlier—it will have to reestablish effective state governance that is welcomed by communities who feel frozen out or victimized by the state. No amount of brute force will woo Iraq’s Kurds and Sunnis to Baghdad. No amount of brute force will elicit genuine loyalty from the many Syrians who supported or fought with the uprising. The anti-ISIS campaign lent a patina of shared interest to an assortment of powers that are actually in existential conflict with each other. The conflict will continue, to murderous and destabilizing effect, until and unless these Arab states change their entire approach and self-definition. That’s a tall order, but it’s the only alternative to endless war and fragmentation.
Fixing the West/Reforming the EU
Yanis Varoufakis
[Published in The Boston Globe Ideas section.]
WHEN THE PUBLIC is disillusioned with an entire political culture, it’s not a problem that technocrats alone can fix. But an unlikely band of Greek reformers may have an answer for an unsettled Europe — and the entire Western world.
Over the last seven decades, Western Europe, with support from the United States, built a liberal order around lofty goals — peace; stable, elected governments; open economies; and shared solutions to regional and global needs. Today, though, Europe’s institutions inspire as much frustration as admiration, with many questioning the entire conceit of a united continent. In the European Union today, citizens heap disdain on the experts in Brussels who have produced reams of regulations on everything from mine safety to banking hours to what kind of labels cheesemakers can use. The sense of malaise ballooned after the 2008 financial crisis exposed the cracks in the union’s foundation, and still more after a wave of new migrants arrived from the south and east beginning in 2015.
While the Brexit vote and the emergence of Donald Trump have prompted some in Europe to rally to the EU’s defense, a homegrown extreme right has gained influence by opposing immigrants and the European Union alike.
Over the years, Europe’s solution to many woes has been to elevate technocrats to ever-greater positions of power, enabling them to go around populist politicians. Yet according to a newly energized wave of reformers, Europe’s penchant for experts has been its undoing, breeding a culture of contempt for democracy.
“We have a Europe that has lost its democracy and legitimacy and soul,” said Yanis Varoufakis, the former finance minister of Greece and founder of the Democracy in Europe Movement 2025, which is trying to invent a new kind of transnational politics that will revive Europe. “We want a European democratic union. Otherwise everything we care about will go to the dogs.”
His movement has attracted 100,000 members and is promoting what it calls a “European New Deal,” modeled after Franklin D. Roosevelt’s New Deal.
The activists in Varoufakis’s movement, also known as Diem 25, argue that if Europe is to survive and thrive, it needs to preserve its social-welfare values but also its capitalist dynamism. Their version of the New Deal would stop austerity policies, beef up anti-poverty programs, and invest in jobs for the unemployed.
Yet Varoufakis’s movement also thinks Europe needs an injection of American-style participatory democracy. Brussels operates by bureaucratic consensus. Diem 25 favors a pan-European government vested with more tangible, but also politically accountable, power.
Supporters of Diem 25 see their struggle as part and parcel of a global response to a crisis of inequality and illiberalism that connects them with Bernie Sanders in the United States and the Podemos party in Spain, and with more hardline constituencies like the Occupy movement and anarchist movements.
Varoufakis and his supporters aren’t revolutionaries. They want to channel a neglected group: the fed-up, left-behind 99-percenters who are angry at bankers, fat cats, and Davos grandees — but who also prefer to fix the system rather than blow it up. The Diem 25 movement wants to harness the energy and tactics of the radical left — but in service of a reform agenda that seeks to repair capitalism rather than replace it.
ALREADY, DIEM 25’S rhetoric is reflected in mainstream policy — in the grudging support for EU reform from German Chancellor Angela Merkel and in a more rousing call for reform this past week from France’s young new president, Emmanuel Macron. “The Europe we know is too weak, too slow, too inefficient, but only Europe gives us the capacity to act on the world stage in the face of the big, contemporary challenges,” Macron said in a speech that endorsed many of the Varoufakis bloc’s proposals
It’s striking that the vanguard of European reform has its roots in the tribulations of Greece. One of the EU’s smallest and weakest members, Greece knows how the union operates at its best and at its worst. Europe integrated Greece in 1981 to rekindle democracy there after a disastrous military dictatorship that fell in 1974. The ancient birthplace of democracy embodied the EU’s role of spreading not only wealth but freedom.
But when the financial crisis hit in 2008, it was every nation for itself. Rich countries in the euro zone, like Germany, had very different needs than poorer peers like Portugal, Spain, and Greece. A cabal of mostly unelected finance officials from rich Europe orchestrated a bailout for poor Europe, imposing draconian austerity and triggering a human calamity. Greece suffered the most, but other poor European countries also languished in depression. Meanwhile, immigrants flooded into a fractured Europe unable to coordinate its immigration policy or control its borders. Eventually a deal was reached that amounted to Europe paying Turkey to bottle up refugees there.
In tatters was any pretense of democratic international consensus. Extremist right-wing groups surged in popularity, while legacy national political parties and the bureaucrats in Brussels seemed out of ideas and popular appeal.
But just in the last year, a surprisingly vital third-way reform effort has surged. Varoufakis, an iconoclastic Greek economist, embodies this new fusion of radical and center. The 56-year-old career academic grew up as a self-identified radical and leftist. As a teenager he sided with socialists against the remnants of Greece’s right-wing junta. In the 1980s, he joined workers on the picket lines in England protesting against Margaret Thatcher’s austerity. By the 2000s, however, Varoufakis had adopted a strikingly centrist ideology.
Even before the 2008 financial crisis, he had begun writing extensively about the problems of runaway finance capital and of central banks more powerful than elected politicians. Yes, communism had failed spectacularly, as the demise of the Soviet Union in 1991 made clear. But triumphalist capitalism suffered its own catastrophe in 2008, Varoufakis believes, opening the path for a renewed social democracy and a heavily regulated version of capitalism.
Fresh off the publication of two books about the perils of global finance and his vision for a policy that preserved capitalism but shattered the hegemony of the elitist 1 percent, Varoufakis found himself suddenly swept from academia into politics in January 2015.
Greece’s new socialist party, Syriza, won power after the country’s established parties all imploded, and drafted Varoufakis to join the government and run its do-or-die negotiations with the euro zone in 2015. For six months, Varoufakis confronted the most powerful finance ministers and central bankers in the world, and made his case to everyone who would listen. Austerity punishes the poor for the incompetence of financial elites, Varoufakis proclaimed.
Europe’s bankers crushed Greece’s attempt to rebel against austerity. Varoufakis left government perversely energized by his failure. He published a tell-all about the secret negotiations to bring Greece to its knees called “Adults in the Room,” with zingers from conversations he had secretly taped on his phone during meetings he’d had with masters of the global finance universe.
The 500-page memoir about the inner workings of currency union and bailouts made an unlikely best-seller. But like Thomas Piketty’s plodding volume “Capital,” it struck a chord with its explanations of the roots of inequality, and alienation — and with its concrete suggestions to improve matters with a hefty dose of electoral democracy and redistribution of wealth and power.
THE DEMOCRACY in Europe Movement 2025 launched in February 2016, with chapters all across the EU. Its acronym is meant to evoke “carpe diem,” the Latin exhortation to seize the day. The year 2025 is the group’s deadline to bring about a new European constitution.
Whenever possible, the movement’s organizers want to persuade existing political parties to adopt the Diem 25 platform, like Poland’s Razem and Denmark’s The Alternative. But Diem 25 will also run for office at the European level; it already is planning a campaign for the 2019 European parliamentary elections.
The New Deal adopted by Diem 25 aims to revive and democratize Europe’s utopian ideals first through quick fixes that don’t require complex international treaties. These include investment in jobs for the unemployed, economic coordination with countries outside the euro zone, and a new digital payments system.
The next steps proposed by Diem 25 are more ambitious. A tax on finance would fund a European budget. The European Commission, which wields enormous executive power, would become directly elected. And the European Parliament, which today lacks even the power to initiate legislation, would become a real legislative body. Existing political parties and new movements like Diem 25 would have to organize and form alliances across national boundaries, creating European-wide electoral politics to complement political life at the national level.
Under current conditions, few European voters would agree to surrender an iota of sovereignty to Brussels; the track record of the technocrats is too tainted. That’s why the first step is to stabilize Europe and deliver big economic improvements using existing institutions and power. Once that happens, Europe can convene a constitutional assembly to draft a new charter for the continent.
In today’s West, Varoufakis said, “authoritarianism and incompetence feed off each other.” With existing approaches discredited, he believes Europeans will be receptive to a federal, democratic blueprint to fix the continent — but it only can work if it wins legitimacy at the ballot box.
“We leftists and liberals whose illusions were incinerated — can get together to stop creeping neo-fascism,” Varoufakis said. “Even though we are radicals, we don’t want to see a disintegration of the EU because of all the great things it has brought — peace being the greatest of them.”
Although anti-Americanism has long been in vogue for much of the European left, there is a strong American flavor to the whole European project. Varoufakis unapologetically praises and borrows from what he thinks is most valuable in the American democratic tradition. It was American pressure, vision, defense, and money that created modern Europe in the first place.
THERE ARE countless hurdles to a reform agenda for Europe. Since the 1950s, efforts to democratize decision-making, or implement real shared sovereignty across national borders, have foundered because member governments, and sometimes their citizens, are loath to shift power to international bodies.
“This idea of the disconnect between elites and the population is widespread,” said Susi Dennison, a senior fellow at the European Council on Foreign Relations who studies efforts to reform the EU.
Some proposals have gained mainstream momentum, she said, including the plan to create some new European parliament seats that are elected by continent-wide votes, and to make the European Commission and presidency more directly tied to elections.
But nationalist sentiment remains strong, as does resistance to the fundamental idea of the EU, she said. As Brexit showed, not that many voters care about the idea that the EU is an effective insurance policy against continental war — even if it’s true. Over time, Dennison said, she fears that even well-meaning reform efforts will appear to the public as nothing more than added layers of bureaucracy, and the European project will lose what little value it retains in the eyes of the public.
“I don’t think it will collapse tomorrow, but there’s a very real risk,” she said.
The slow-boil crises of the last decade have altered the landscape throughout the United States and Europe, with anti-immigrant right-wing groups an established part of the political power structure. For the latter half of the 20th century, Western electorates might have come to see war as a risk only for faraway, far less fortunate countries. But the tensions that have erupted since 2008 serve as a reminder that the West’s democratic peace isn’t a given. It arose from the aftershocks of apocalyptic world war, and took sustained effort to build. Without strong public commitment, it could crumble.
Strengthened by War, Hezbollah Displays Regional Power
PHOTO: HEZBOLLAH TROOPS IN OUTSKIRTS OF FLITA, JULY 26. SOURCE: WAR MEDIA CENTER.
[Published at The Century Foundation.]
By Thanassis Cambanis and Sima Ghaddar
Hezbollah’s battle against ISIS and like-minded jihadis this month has not attracted as much attention as the ongoing campaigns in Raqqa and Mosul, but it signals an important shift in the Middle East order.
At the end of July in less than a week, Hezbollah quickly dislodged a jihadi stronghold on the border of Lebanon and Syria in the Lebanese town of Arsal. Significantly, Hezbollah, or the Lebanese Party of God, orchestrated a long political and public relations campaign before the offensive, and ultimately put together a military campaign that featured a strange, but effective coalition of government armies essentially led on the ground by a transnational non-state actor.
In this case, Hezbollah quarterbacked a campaign that featured its troops, battle-hardened after five years on the front lines in the Syrian conflict, fighting with support from the Syrian and Lebanese militaries. Hezbollah and the Syrian armed forces have been working together closely for years, but Hezbollah’s partnership with the Lebanese military is more circumspect. Hezbollah and the Lebanese Armed Forces coordinate extensively but zealously guard their autonomy. To boot, the Lebanese army receives extensive support from the United States, which considers Hezbollah a terrorist group—making it all the more pressing for the Lebanese army to keep its distance from Hezbollah.
All these factors make the July offensive in Arsal all the more remarkable. Lebanon’s Sunni prime minister Saad Hariri, who is an outspoken critic of Hezbollah’s regional expansion and role in Syria, ultimately signed off on an operation which highlighted the new balance of power emerging in Lebanon and the Levant.
Hezbollah, arguably, played a more pivotal role than any other Syrian ally in keeping Bashar al-Assad in power when his rule was threatened by the uprising that began in 2011. Since then, Hezbollah has grown more open about its role training and sometimes fighting with militias in Yemen, Iraq, and Syria—a regional expansion that it has undertaken in tight partnership with Iran.
Western Perceptions
The United States and western countries have maintained a hard rhetorical line against Assad and Hezbollah—but at the same time, have clearly decided they prefer Assad’s alliance to the alternative. Early in the Syrian war, Assad and Hezbollah presented themselves as the pluralistic, religiously tolerant bulwark against Sunni Islamist fundamentalist jihadis. That might have been a misleading description in 2012, but now—in large part because of the Syrian regime’s starvation sieges and a Western failure to support non-jihadi rebels—that binary has edged closer to the truth.
Hezbollah’s dual role might make Western governments uncomfortable, and it might force them to undergo rhetorical gymnastics in order to continue their relationship with Lebanese state institutions while ignoring the reality of Hezbollah’s central role in the state and the region. However, it is nonetheless true that Hezbollah has emerged from the disarray in Syria as an indispensable national and regional actor with reach, strategic vision, and capacity. That’s why Hezbollah, and not the Lebanese army, led the campaign to liberate Arsal from jihadi fanatics who have held sway there since 2014.
Hezbollah’s Coalition
On Thursday, Hezbollah Secretary General Hassan Nasrallah declared victory in Arsal. “We are doing our victory and expect no victory,” he said. He also ignored the previous day’s press conference in Washington, in which President Trump appeared to believe that Lebanon was fighting to disarm Hezbollah, rather than fighting alongside Hezbollah to disarm Al Qaeda.
The details of Lebanon’s campaign against Al Qaeda, ISIS, and other jihadists are important. So too are the complexities of America’s relationship with the Lebanese state and its institutions, which ought to be reinforced despite their deeply intertwined and sometimes ambiguous relationship with Hezbollah. Even more important, however, is the strategic picture that has been getting clearer and clearer as the war in Syria has progressed toward a resolution that favors Assad’s government and his allies: Hezbollah, Iran, and Russia.
Hezbollah’s campaign in Arsal holds important clues to the regional order taking shape as the war in Syria winds down and new coalitions fill the vacuum created by an America’s growing distance. A mature, transnational Hezbollah quarterbacked a delicate and tense offensive that in practice coordinates two national armies that would appear nearly impossible to place in the same order of battle: the Lebanese national army, whose main supporters these days are the United States and Great Britain, and Bashar al-Assad’s military.
Emerging as a Regional Leader
The coalition in Arsal is a remarkable bellwether for several reasons. It showcases Hezbollah (and by extension, Iran) in a leadership role in an anti-terror coalition. For years, Hezbollah has been trying to persuade Western governments that it is a natural partner in the global campaign against extremist groups that tend to come from the Sunni takfiri milieu. The campaign also formalizes the de facto balance of power in which Hezbollah operates autonomously in both Syria and Lebanon—and in which Hezbollah has enough political sway to set terms for governments in both Damascus and Beirut.
The battle for Arsal holds plenty of clues for the template of Hezbollah’s influence going forward. As a dominant, transnational force, Hezbollah can now hold its own among the region’s nation-states; but as the complex mechanics of its role in Arsal underscore, it is also not a giant, able to dictate terms to those around it. It had to wait and assuage concerns from political and military leaders, in order to persuade the Lebanese army and the Lebanese government to get on board with an offensive that would be perceived in some communities in sectarian terms, as an anti-Sunni attack by a Shia coalition. Hezbollah has displayed strategic patience, biding its time and keeping its eyes on long-term goals that will benefit it organizationally and also help their coalition partners, especially their closest ally and vital sponsor, Iran.
Around this time last year on July 16, 2016 after multiple suicide bombers snuck from the outskirts of the Lebanese northeastern border town of Arsal and targeted the northern village of Al-Qaa, Hassan Nasrallah, Hezbollah’s secretary general, said Lebanon is in dire need of an official national defense strategy to fight terrorism. When “others” abandon their responsibilities, he then added, people must assume the responsibility to protect themselves. “The responsibility of the state is our responsibility too,” he said, but always alongside the Lebanese Army and the Lebanese security apparatus.
Since its intervention in Syria, Hezbollah has glorified the role of the Lebanese Army in fighting terrorism in the outskirts of Arsal, but has dictated and directed the terms and conditions of that fight knowing very well the army cannot handle a heavy load and is dependent on both British and U.S. funding. For months now, Hezbollah has independently negotiated settlement deals with an opposition group at the outskirts of Arsal and neighboring Qalamoun region, known as Saray Ahel Al Sham, to relocate refugees and arbitrate with the terrorist groups, Hay’t Tahrir Al Sham (Al-Nusra) and ISIS. However, to no avail. Hezbollah came under attack after Nasrallah recently pledged to clear the town’s outskirts of Syrian militants and rebels with a coordinated air raid campaign by the Syrian regime.
Through all these crises on the border, Hezbollah has steadily built its capacity and deepened its relationships with institutions and governments, making clear that it is de facto a peer, rather than a player in a less significant category simply by dint of being defined as a non-state actor.
When Hezbollah dived headlong into Syria’s civil war, many observers of the Middle East wondered whether the adventurist gamble would the undoing of the Lebanese Party of God.
Instead, it appears that five years of open international warfare have strengthened Hezbollah’s regional position, consolidating its transnational military and political organization. The Party of God entered the Syrian war as a dominant force inside Lebanon; it appears set to emerge from it as a decisive regional player, likely to be as powerful in the coming period as most of the Middle East’s full-fledged states.
TCF World Podcast: Demythologizing ISIS
In TCF World’s inaugural podcast episode, Century Foundation fellows Thanassis Cambanis, Michael Wahid Hanna, Aron Lund, and Sam Heller try to put to rest some of the mythology and exaggerations that have grown up around the Islamic State (also known as ISIS). After three years of power in a self-declared caliphate, ISIS is on the run from Mosul, its capital in Iraq, and is on the verge of defeat in its Syrian stronghold of Raqqa. Nonetheless, many commentators and U.S. policymakers still contend that ISIS is as powerful as ever, and is winning even while appearing to lose. The Century Foundation’s foreign policy team considers drivers of the Islamic State’s resilience and resurgence, its actual strengths and potential, the impact of territorial losses, and the fragile commitment of some governments to exterminate ISIS.
Link: https://tcf.org/content/commentary/tcf-world-podcast-demythologize-isis/
ISIS was a symptom. State collapse is the disease
An Iraqi Counter-Terrorism Services member prays in the Old City of Mosul on July during an ongoing offensive to retake the city from Islamic State group fighters. FADEL SENNA/AFP/GETTY IMAGES
[Published in The Boston Globe Ideas.]
The collapse this month of the Islamic State, also known as ISIS, has been greeted with joy and relief in many quarters, especially among the millions of civilians who directly suffered the extremist group’s rule. Much of the predictable analysis has focused on long-term trends that will continue to trouble the world: the resonance of extremist jihadi messaging, the persistence of sectarian conflict, the difficulty of holding together disparate coalitions like the clumsy behemoth that ousted ISIS from its strongholds in Raqqa and Mosul.
But jihadis and sectarians are not, contrary to popular belief, the most important engines of ISIS, Al Qaeda, and similar groups. Nor are foreign spy services the primary author of these apocalyptic movements — as many around the world wrongly believe.
No, the most critical factor feeding jihadi movements is the collapse of effective central governments — a trend in which the West, especially the United States, has been complicit.
An overdue alliance of convenience mobilized against the Islamic State three years ago, but only after leader Abu Bakr al-Baghdadi had taken over enough territory to declare statehood. The ISIS caliphate was as much as a state — for as long as it lasted — as many other places in the Middle East. Most of the coalition members detested ISIS, but only the local members from Iraq and Syria whose families were dying or suffering under Islamic State rule were fully invested. For the rest of the anti-ISIS coalition, fighting the caliphate was one of many other priorities.
The glacial, slow-moving, coalition united against ISIS but bound by little else. It is sure to dissolve quickly now that the emergency is over.
Secretary of State Rex Tillerson called the defeat of the ISIS caliphate a “critical milestone,” and Iraqi prime minister Haider Abadi hailed “the failure and the collapse of the terrorist state of falsehood and terrorism” that ISIS had proclaimed from Mosul. Yet even as the partners cheered the defeat of one state, they acknowledged the need to rebuild another one — Iraq — if they want to avoid cyclic repetition of the same conflict. Abadi, like American commanders on the ground, described a daunting task: to unify feuding militias, provide services to long-ignored populations, and perform effective police work — in short, to finally extend a functional state throughout Iraq.
In the years since terrorism has become an American obsession, much attention has focused on the root causes of nihilistic violence. The latest iteration of this vague quest, which attracts billions of dollars in government funding, is “countering violent extremism.” But it’s entirely possible that violent extremists aren’t really the problem at all; they only matter in places where the state is too weak to provide security, or too incoherent to explain why terrorist attacks are merely a crime, rather an existential threat.
Here’s another way to put it: There is no after ISIS, because ISIS isn’t the problem. The collapse of states is.
THE MOST EFFECTIVE INFANTRY troops in the war against ISIS, in fact, come from movements whose long-term aspirations are accelerating the collapse of the state order in the Middle East. To be sure, the key fighting groups — the Iraqi Kurdish peshmerga, the Shia militias referred to as the Popular Mobilization Units, and the Syrian Kurds from the PKK — are nothing like ISIS. They aspire to political and territorial power without the murderous, nihilistic sectarianism of the Islamic State. At the same time, these groups all profoundly oppose central government in the areas where they live. Some, like the Iraqi peshmerga, want to form a smaller, independent Kurdish republic, even though they are internally divided in a way that promises future strife and civil wars, not harmony. Others, like the Shia militias, want to carve out an autonomous state of their own that functions in the lee of a hobbled central government.
The United States has contributed mightily to this dismal state of affairs. To solve an immediate problem, ISIS, it guaranteed a still-more toxic long-term problem: an ungovernable zone stretching from the Mediterranean to the Zagros Mountains, where death squads, militants and fundamentalists will continue to proliferate.
And as ISIS taught us well, local problems rarely remain local.
The central problem to face after the ISIS caliphate, then, isn’t whether the Islamic State will return or in what form, but when we’re going to tackle the epochal and complex challenge of supporting coherent states in the Middle East. The United States has been a major catalyst of the current entropy and chaos in the Arab world — sometimes through direct destabilizing actions, like the invasion of Iraq in 2003, and other times abetting long-term corrosion by backing ineffectual, tyrannical despots who ransack their own states in order to cling to power.
Much of the immediate response to the collapse of the caliphate centers on Sunnis, and is cast in simplifying sectarianism. Can their grievances be better addressed, to stop their ranks from breeding foot soldiers for nihilists? Can Shia partisans slake their thirst for power and share enough of spoils to coopt disenfranchised Sunnis?
There are some important points nested in this type of analysis, but it overlooks one essential fact: Factors like sectarian identity, jihadi extremism, and mafia corruption only become dominant pathologies in areas where the state is no longer fully in control. The Islamic State can claim adherents in dozens of countries. But an Islamic State insurgency only rises to central importance where a failing state has left a vacuum.
The glacial, slow-moving, coalition united against ISIS but bound by little else. It is sure to dissolve quickly now that the emergency is over.
Compare, for example, the ISIS campaign in the Levant, where Abu Bakr al-Baghdadi established his short-lived state, to the far less potent Islamist insurgency in Egypt. Sure, followers of the Islamic State have murdered civilians, attacked state targets, and created limited mayhem in parts of Egypt — but the Egyptian government and security services remain powerful and as much in control as they ever have been.
State narratives and identity also limit the power of the nihilist narrative. Governments in Iraq and Syria struggle to convince all their citizens that the state functions everywhere and cares for all its citizens. But ISIS attacks on civilians in places like the United Kingdom, France and Egypt, cause consternation but don’t raise questions about the very viability of those states.
The Islamic State is a murderous movement. The existential threat comes not from ISIS but from state failure — a failure that precedes, rather than results from, the rise of violent fundamentalists.
THE ISLAMIC STATE MADE a great fuss about tearing down the old borders drawn by colonial powers. Many groups that otherwise detested ISIS shared the extremists’ distaste for the artificial borders that divided historical neighbors and cobbled together problematic, hard-to-govern entities.
That discussion about viable borders, however, created confusion. Some took the rise of ISIS as evidence that the nation-state itself had entered the final state of eclipse. That view dovetailed with a fascination that grew since the end of the Cold War among some academics and futurists, who believed the global order had transcended the era of states.
In its most breathless incarnation, pop theorists like Parag Khanna celebrated a “nonstate world,” in which states were just one of many players happily competing with free-trade zones, corporations, cities, empires and other levels of organization to maximize utility.
More reserved scholars also concurred that we had entered a post-state era. Some argued that the future held more shared-sovereignty projects, like the European Union, in which states would give up power in exchange for the efficient and humane economies of scale offered by supra-national institutions. Utopian internationalists like Strobe Talbott wrote warmly of a “world government” in which scientific management principles would replace parochial nationalism.
Pessimists agreed that the state was in irreversible decline, but believed something worse would take its place: tribes, militias, unaccountable local strongmen, and predatory companies.
The conflicts since the Cold War point toward a different struggle, between strong and weak states, rather than between states and some mythical nonstate world.
At West Point after the 9/11 attacks, George W. Bush declared the world had already resolved the struggle against totalitarian ideologies during the 20th century. “America,” Bush said as he unleashed a series of wars that continue 15 years later, “is now threatened less by conquering states than we are by failing ones.”
A case in point is ISIS, which was in fact enamored and obsessed with a very traditional view of power and statehood; their project wasn’t to erase the state, but to invent a new one.
The nation-state is a relatively new phenomenon, dating back just a few hundred years. But states need not be based on nationalism. In fact, the most resilient and powerful states have often stoutly rejected a nationalist identity, instead embracing an identity based on empire (Britain), geographic scale (the United States), or continuous civilization (China).
“The state continues to be the basic building block of politics. Fragile states don’t diminish that fact,” said Alasdair Roberts, incoming director of the school of public policy at the University of Massachusetts Amherst.
Two years ago, Roberts argued that after brief period of uncertainty, the last few decades had shown that states remained the seat of power, in an essay called “The Nation State: Not Dead Yet.”
In the United States, critics of globalization feared that America was surrendering power and sovereignty to organizations like the World Trade Organization. Roberts says that recent developments, especially since the election of Donald Trump, proved what many politicians had said all along: “We’re delegating authority, and if we want to get it back, we can get it back.”
A strong, functional state might subcontract authority to the United Nations, or to an oil company, if such an arrangement suits the state’s interests. But all across the world, in rich countries and poor, states have quickly reclaimed their prerogatives when they believed their national interests were threatened by a trade agreement or an international court decision.
In our times, the Middle East has been the world’s biggest exporter of militants and destabilizing violence.
But the Middle East is not inherently violent or unstable. States have managed to assert authority and control their territory — although sometimes in savory ways — at many points in modern history. Governments in Turkey, Iran, and Arabian Gulf maintain a monopoly of force and a passable piece, ruling ethnically diverse populations (although with limited political rights for citizens). Flashpoints like Syria and Yemen knew stability for many years during the last generation. State-builders like Kemal Ataturk and Gamal Abdel Nasser reversed periods of decline and fragmentation, showing that it’s possible to bring unity and extend the reach of a bureaucratic state even in unruly and poor places.
We are living with the results of failing states in the Arab world. The best alternative is to see them replaced with functional ones. In some cases, that might mean holding our noses and accepting effective but cruel leaders. In others, it will mean exerting pressure and sometimes using force.
It doesn’t work to waffle, as Obama did when he tepidly supported the Arab uprisings in only some countries, and then just as tepidly stood by some of the dictators who mercilessly crushed popular revolts. It also doesn’t work to confuse tyrants who stay in power while eviscerating the state, like Gaddafi in Libya and Saddam in Iraq, with distasteful rulers who maintain a functioning state and are therefore effective, like the Saudi monarchy.
For the United States, a smart policy requires commitment. We know Bashar Assad will never create a sustainably stable government in Syria, because of his determination to wipe out rather than coopt dissent. Iraq is less straightforward; the United States cannot stand by passively as the state breaks up. But that requires clearly choosing sides: openly support Kurdish secession, and division of Iraq into smaller, ethnic or sectarian states, or openly repudiate the Kurdish drive toward independence and put pressure on Baghdad to extend its writ. The current course of intentional ambiguity only promotes the worst alternative — state decline.
When possible, we ought to promote humane governance. But in all cases we must insist on effective state power. We have seen the alternative in Iraq, where the United States and other guarantor powers, including Iran, let the government in Baghdad decay, only intervening when ISIS took control of nearly one-third of the country.
A state that is both cruel and ineffective is an albatross for the whole global order. If we want to counter violent extremism, we’re going to need a world of effective governance — and for now, the only place that’s likely to come from is strong states.
Only Humane Governance Can Erase Legacy of ISIS
[Published at The Century Foundation.]
This summer, the Islamic State will probably lose its capitals in Syria and Iraq, and possibly, any hope of surviving as a traditional territorial state. For three years, however, the ISIS caliphate functioned as a state—blood-trenched, appalling, and wildly unpopular—but a state nonetheless.
Its fall certainly doesn’t preclude other jihadi movements from replicating Abu Bakr al-Baghdadi’s feat in the future. And the Islamic State’s material success highlighted just how awful many other governments in the region are. Too often, Middle Eastern states tolerate rampant torture, repression, surveillance, and rights-stripping; the nihilistic horrors and excesses of ISIS weren’t categorically different, but they took these practices to another level.
With the Islamic State downgraded from contender state to insurgency, we now would do well to ask: What is the best long-term antidote to extremist violence?
The answer might lie not in countering violent extremism, but in investing in strong states. And crucially, our experience with state failure and abusive governance in the Middle East should force us to update our definition of a strong state. It is not, as American policy makers have historically believed, a state ruled by a strongman willing to accept phone calls from Washington.
In actuality, a strong state is one that effectively controls its territory and governs its citizens, providing stability and continuity though humane rule and rights for its citizens. Any state that rules through caprice and violence is inherently unstable, even if it possesses a monopoly of force within its borders. Such are the lessons of the failed and failing states of Arab region, whose erosion has allowed violent extremism to flourish. To significantly reduce extremist ranks, it does not suffice to target individuals. A country has to build (or rebuild) an alternative to authoritarian thuggery: a bureaucratic state and security services that actually provide security rather than repress citizens.
Effective governance means humane governance. Anything else is a short-term fix.
Fighting the Wrong War
There are two things that the West, and primarily the United States, must grapple with in order to reverse the jihadi tide that will continue to lap at its shores long after Abu Bakr al Baghdadi’s Caliphate recedes as a grisly but mercifully short chapter in geopolitical history.
First, we need to embrace robust liberal pluralism as our most potent weapon against the ideology of jihadi nihilism, violence, and intolerance. Over the long haul, the West’s openness, prosperity, and education make for better societies than anything on offer from repressive religious extremists or Middle Eastern despots. Not only should we refrain from apologizing for this characteristic; we ought to tout it as the leading edge in our counter-extremism campaign.
Second, we need to admit that our misguided foreign policy and indiscriminate use of violence in the wars against terror since 9/11 have bred a great deal more outrage, extremism, and terror than they have contained. We might not have created the problem, but we have definitively made it worse. We continue to employ the same fruitless “capture, kill, contain” techniques, to our continued disservice. As a result, the cancer that presented as the “caliphate” will in due course metastasize somewhere else.
The prime candidates for the next outbreak of hypertoxic jihadi extremism are places where the United States, or allies with its support, are creating famine, mass displacement, and wantonly killing civilians—while supposedly pursuing extremists, using the hard-to-monitor blunt weapons of aerial bombing, drones, and special forces.
Such battlefields, sadly, exist today in places that only occasionally draw attention, like Yemen, Libya, and Afghanistan, and also in more uniformly ignored war zones in places such as Mali and Nigeria. Declining and eroding states have opened the gates to extremists of all sorts in a long list of poorly governed spaces, including parts of the Sinai, Somalia, South Sudan, Lebanon, and the Philippines.
Embracing Conflict and Despots
By the end of his time in office, President Obama was deploying U.S. special forces simultaneously to 139 countries—that is, two-thirds of all the countries in the world. Not all of those deployments were active conflict zones, but the United States is fighting in undeclared wars in several, including Syria and Yemen. Endless war only serves to weaken states—the very things we need in order to live in a secure world.
The coalition against ISIS relied on nasty alliances of convenience with dictators, authoritarians, and militiamen, many of whom were in thrall to sectarianism and bloodlust. This devil’s bargain is the same principle that guided the Obama administration’s clumsy embrace of the Gulf Cooperation Council monarchs and their war in Yemen, and which drives the Trump administration’s much warmer embrace of Arab despots.
In his debut foreign trip in May, President Trump cast aside any pretense of valuing democracy or decency in our allies. “We must seek partners, not perfection—and to make allies of all who share our goals,” President Trump told the heads of state assembled in Riyadh.
Trump echoed the refrain of the region’s despots, who self-servingly claim that their failing brand of governance is the only alternative to the Islamic State and its imitators.
“Our partnerships will advance security through stability, not through radical disruption,” Trump said. “Wherever possible, we will seek gradual reforms—not sudden intervention.”
History might prove him wrong, but he was only saying out loud a view privately shared by many of his White House predecessors. Iran was the only state singled out for doing anything to promote terrorism, as if state policies adopted by American allies, including Saudi Arabia, Qatar, Iraq, and Egypt, had played no role in abetting violent extremists.
This mistake has become a cornerstone of American foreign policy, repeated over and over again. If unshakeable support for despots provided insurance against runaway violence, today we’d be living in a quiet, peaceful world. It’s not just that devil’s bargains are distasteful and betray our core values; they also don’t work.
Only effective, humanistic states provide an alternative to a governance wasteland that promotes apocalyptic preachers and young people who embrace death in the absence of a sustainable future.
Short-Term Fixes
States in the Middle East and North Africa region are failing. Successful states must exercise their authority over, and elicit loyalty from, a plurality of citizens. Even homogenous states are to a certain degree multiethnic and multisectarian. Difference must be managed, not ignored or suppressed.
Such states have been built before in the Middle East, and have prospered. Even in today’s dark period, there are plenty of states that muster a significant degree of state authority and competence. Egypt, until recently, was an example of how a flawed state could still perform most of its core executive and security functions.
It’s a debatable proposition that authoritarians are the answer. History suggests that sometimes authoritarians can be effective long-term leaders. Their success depends on resources, competence and a commitment to results. Gamal Abdel Nasser was no democratic civil libertarian, but he was genuinely invested in modernizing his country. For decades, he delivered results that seemed to mitigate his authoritarian tendencies. Toward the end of his rule, the balance had shifted—an increasingly erratic and paranoid Nasser presided over a state that stagnated economically and no longer proved capable of securing its borders. Hence a period of domestic paralysis coupled with the catastrophe of the 1967 war.
There are plenty of other examples, ranging from the resurging conflict in southeastern Turkey to flare-ups in rural Tunisia, to suggest that a cloak of stability thrown over incompetent rule and mass repression is only a short-term fix: the simmering violence in every Middle Eastern conflict zone testifies to it.
In the post-colonial Middle East, we mostly see weak states. Policymakers by necessity often focus on the crumbling and collapse, since they cause the biggest problems. But let’s not forget that the reverse is possible. A strong state, an effective state, even a decent state, can be imposed in a country that appears in the grip of anarchy and chaos. It’s happened before and could happen again.
Must a Strong State Be a Just State?
A state that succeeds as a state provides basic security and services. It can be an awful state in many other regards, usually by abusing minorities or withholding political rights, but consolidated states offer continuity, loyalty and a kind of security that’s been in increasingly short supply. (I have written elsewhere about the resilience of the state as the main unit of analysis; here I want to expand on the possibility that only a humane, rights-based state can provide lasting stability.)
The default—the continuing collapse of states in the Middle East—promises more instability. To reverse the poisonous forces ascendant in the Middle East, states must consolidate power and the impose central authority on the full spectrum of militias and political stakeholders. Otherwise, sectarianism, local warlord rule, runaway mafias, and foreign intervention will continue to steer events in places like Lebanon, Syria, Iraq, and Yemen.
It is possible that a state can succeed without humanism. Saudi Arabia is an excellent test of the proposition. The monarchy offers no pretense of rights, but promises to take good care of its citizens. The most colossal failures in recent times, like Bashar al-Assad, Saddam Hussein, and Moammar Qaddhafi, failed not because of their egregious human rights abuses but because they hollowed out the state apparatus and lost physical control. So it’s possible that a well-executed, abominable police state can indefinitely keep the lid on a population. The popular explosions in Iraq, Syria and Libya, however, suggest that brute-force repression is always a temporary solution.
But for a state to truly thrive, it needs to address the basic needs of its people, which include a modicum of political rights. Otherwise they will not be invested in the state which rules them. We need new, better models of governance, which are inclusive and provide genuine political feedback. They need not look just like Western democracies. Nor, however, can they trample their people’s rights. Citizens in the Middle East, like everywhere else in the world, demand decent treatment from their government, and they expect some say over how they’re ruled. They also have a historical memory of times and places when different identity groups coexisted without violence, as well as when political loyalties came with dividends—and not merely with the threat of reprisal against the disloyal.
The long-term recipe for a Middle East free from the scourge of violent extremists is the same as it is everywhere else: effective rule by states both strong and humane, that recognize pluralism, rule of law, and human rights.
COVER PHOTO: TWO MEN CARRY SICK AND INJURED CHILDREN TO SAFETY THROUGH THE RUBBLE OF A STREET IN THE OLD CITY OF MOSUL ON JUNE 24, 2017. © UNHCR/CENGIZ YAR.
Let’s Make a Deal: Emerging Global Trumpism
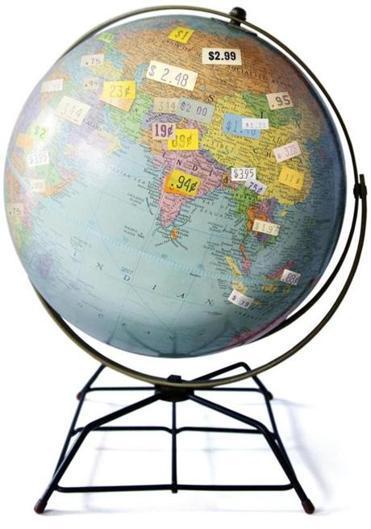
Illustration: ROB DOBI FOR THE BOSTON GLOBE
[Published in The Boston Globe Ideas.]
DONALD TRUMP came into office promising that his sharp deal-making skills would revolutionize US foreign policy. It sounded like bluster — not much of a change from Trump’s predecessors, who also believed they were negotiating deals for their American constituents.
To many ears, Trump’s vow also sounded unprincipled. Even though American relations with the rest of the world always have had a transactional element, Washington’s overarching goals for most of its history have been broad and moralistic, with a premium on long-term security and prosperity.
Meanwhile, Trump’s initial moves — dispensing with the niceties of alliances and accords, breaking with normal diplomatic practice, avoiding the theater of give and take before critical decisions are made — seemed to reflect his impulsive temperament, not some larger theory of how to promote the national interest.
But after a hectic half-year during which Trump has thrown the US diplomatic handbook out the window, the rough outlines of Trump doctrine are starting to emerge. Even the president’s most vociferous and worried critics (myself included) ought to entertain the prospect that there’s a method to the recent madness in international affairs. Maybe Trump’s wholesale reengineering of America’s approach to the world isn’t just the accidental consequence of a White House managed by chaos theory. Maybe Trump really has an intentional plan to transform the world order itself.
In recent weeks, Trump has begun to articulate what “America First” deal-making means on the global stage. Announcing his withdrawal from the international climate change accord, he emphasized that he represents “Pittsburgh, not Paris.”
Still more telling was his speech in Saudi Arabia, where he assured a select group of pliant allies that America would stop lecturing about rights and responsibilities . He also signaled he would support an unpopular war on Yemen, and take sides with Saudi Arabia in its other neighborhood squabbles with Qatar and Iran, so long as Saudi Arabia adopted America’s counter-terrorism priorities and continued its historical support of the US defense industry. While the president appears to have exaggerated a colossal $110 billion arms deal with Saudi Arabia, the contours of Trump’s deal were clear.
Bald nativism colors the president’s rhetoric, but a clear ideology underlies it. Trump’s government will no longer shoulder a superpower’s burden of maintaining a world order; it will leave that task to others, and reap the short-term windfalls that might come with its collapse. Transactions will no longer be a tactic but the goal itself; each interaction must be a win for the United States — no more short-term compromises to achieve long-term goals. His predecessors made soaring appeals to the aspirations of free peoples. Instead, Trump asks at each and every turn: “What’s in it for us?”
This approach has several virtues for Trump. It can be explained on a bumper sticker, unlike more ambitious policies, which by definition are also more ambiguous. Its gain will come in measurable increments — big arms deals with a set price tag, big savings for American businesses no longer fettered in the international arena by rules and regulations — and not in hard-to-quantify metrics like stability, thwarted terror attacks, or democracy. Finally, the Trump approach is all about the now. How do you sell the American public on achievements like balancing a chaotic Middle East in order to stave off worse future violence, or protecting global shipping lanes, or upholding the NATO alliance?
Trump knows how to sell, and those of us who cherish the international liberal order (which until recently was a public good with profound bipartisan support) must worry that Trump’s foreign policy doctrine could win many adherents in the United States. His maneuvers will be understood to save money, dodge entanglements, and earn respect. So what if they actually do the opposite of the course of a full presidential term? Trump might build the most successful isolationist coalition in American history — in large part because he’s not a pure isolationist.
He wants to retreat from international commitments, and is willing to explode norms and institutions that make the world safer and richer, but he doesn’t want to retreat from the world itself. He’s happy to get involved, piecemeal and opportunistically, to make a buck here and a splash there. In Syria, for example, he has resorted to shows of force that Obama eschewed, twice bombing Syrian government targets, but he’s also shelved most of the sustained efforts by the Pentagon and State Department to actually manage or contain the Syrian conflict. This approach is not pure isolationism, but it is chauvinistic and indifferent to the needs of America’s allies (and the capabilities of its enemies to cause problems). Even as it harms America’s long-term standing and interests, Trump’s approach might well reap some short-term political wins that boost his popularity among Americans who have always been ambivalent about their superpower role.
FOR AT LEAST a century, America has conceived of itself as a “great power,” a primary beneficiary of a world order that it creates and upholds. During some periods of history, the global order is fluid, and it’s every nation-state for itself; in other, steadier times, there’s a firm taxonomy. Major powers set the terms for everyone, and reap most of the benefits. Most smaller powers accept the role of client, while a few maximize their interests by acting as spoilers, refusing the terms of the dominant order and risking a forceful response from the main powers.
Traditionally, America has pursued its interests with an eye on the long term, forgoing quick gains in order to consolidate positions that are perceived as best for American security and prosperity. Strategic patience has governed policy moves that are visionary as well as appalling. America made great sacrifices to rescue Europe during two world wars, and invested impressive resources through the Marshall Plan to ensure Europe’s post-war recovery into a wealthy zone of peace. America was equally long-sighted, if considerably less altruistic, in pursuit of Manifest Destiny and the Monroe Doctrine, which gave America a continental scale and ensured its domination of the Western Hemisphere, at an awful cost to indigenous Americans and the political autonomy of its neighboring countries. For good and ill, America was trying to control the game board, not merely to win the next round.
During the Cold War, although American foreign policy was complex, its central stated goal was straightforward: contain communism.
Trump’s emerging transactional doctrine harks back to that Cold War simplicity, after 25 years during which American presidents from both parties struggled to articulate precisely what American foreign policy stood for. The simplicity of Trump’s doctrine might feel familiar, but its innovation is to divorce America’s calculus from any core principle, moral or strategic.
American foreign policy has, since World War II, embraced liberal internationalism. The most important rival view has been classical realism, which would strip away moralistic layers of policy, like democracy promotion and humanitarian intervention, but would still exhort America to engage in promoting a stable world order that safeguards American interests. Realism — as practiced to some extent by states like Britain, Germany, Russia, and China — is less sentimental than liberal internationalism, but it invests heavily in cooperative international institutions, regimes, and agreements that preserve national interests. Meanwhile, from the margins, isolationists argue that America can protect itself without any truck with foreign powers and international accords.
Trump’s approach doesn’t fall neatly into these categories. It’s clearly anti-internationalist, but it’s not isolationist. Its closest historical analogue is the dangerously ambitious and agnostic approach of rising powers like Germany and Japan in the early 20th century, who were struggling to elbow their way into an international order that actively excluded them. There are few parallels of a strong, rich, established power resorted to destabilizing, relentless opportunism.
Unsurprisingly, Trump’s foreign policy doctrine is anathema to liberals, and it’s being executed in a haphazard and dangerous way. But it also draws on some real interests, often overlooked by liberal internationalists — like demanding that NATO allies shoulder their share of communal defense, or calling out Iran on its belligerence, or admitting what has already been a long-time practice: The United States will quickly overlook human rights abuses by countries that are willing to make lucrative deals with American companies.
A cynic might argue that there’s no real danger, since America’s foreign policy was often transactional in the past, and that Trump is simply saying in public what past presidents preferred only to discuss in private. But such insouciance overlooks the novelty of opportunistic transactionalism elevated from occasional tactic to core doctrine.
AS SOON AS America defects from international accords, others will follow suit or step in to fill the void. Some of these accords are informal, like America’s long-term commitment to promoting a balance in the Middle East rather than throwing its lot in wholesale with one side in a regional war. Trump has effectively thrown in his lot with one faction, dominated by Saudi Arabia, and the region is sure to witness an uptick in violence along with an increase in foreign involvement. Others, like NATO or the Paris Agreement, attempt to codify and lock in international cooperation in order to achieve ambitious goals that no single nation can accomplish alone but that benefit all. Without America’s support, it’s unclear whether such initiatives can survive, but by quitting (or in the case of NATO, potentially shirking) America stands to reap the short-term windfalls of the spoiler or the rogue state even if in the long-term it is likely to suffer the blowback as painfully as any nation.
The dangers abroad are manifold. They’ve begun to unfold in the Middle East, as states emboldened by Trump’s transactionalism already are overreaching. Israel’s settlements expand undaunted, and its political leaders (over the objections of its security establishment) are considering the merits of a preemptive war against Hezbollah in Lebanon, which would be disastrous for both Lebanon and Israel. Saudi Arabia, with Trump’s full blessing, is ramping up a war in Yemen that is only accelerating state collapse and terrorism, while pursing a collision course with Iran and any Arab state that deviates from the Saudi line (witness the recent excommunication of Qatar by Saudi Arabia and its partners).
On a global scale, China has quietly stepped into the gap left by the United States, making preparations for a vast web of infrastructure and investment that could make Beijing the key arbiter in East Africa, the Middle East, and parts of South Asia, as well as in the trade routes connecting those regions to China. Russia has asserted itself with new force in its sphere of influence. Rising nations around the world that have played along with international norms will reconsider destabilizing pursuit of self-interest over wider harmony, a state of autarchy and competition that could easily accelerate nuclear proliferation, a breakdown in international trade, and spikes in pandemics, famine and poverty.
A foreign policy that relentlessly maximizes immediate benefits for the United States might have a lot of appeal for Americans, even among constituencies that don’t like Trump. Its short-term results could play well in electoral cycles, before the toxic dividends come due.
At home, Trump’s approach will fan the flames of nativism and isolationism. In recent history, when America turned its back on the world and wished its responsibilities away, cataclysms forced it to reengage, first at Pearl Harbor and then on 9/11. The United States is the most powerful nation in the world. Its actions affect almost everybody on the planet, and, because we all live on the same planet, the actions of others affect the United States. America is dominant, but not all-powerful. It’s a giant on the world stage, but giants and predators do not live in splendid isolation. Their success and survival depend on an ecosystem. If America destroys that ecosystem, it too will suffer the consequences.